A new strain of malware developed by threat actors believed to be affiliated with the FIN7 cybercriminal group has been used by members of the now-defunct Conti ransomware gang, indicating cooperation between the two crews. increase.
malware called dominois primarily designed to facilitate subsequent exploits on compromised systems, such as delivering a little-known information stealer that has been for sale on the dark web since December 2021. increase.
“Former member of the TrickBot/Conti syndicate […] Using Domino since at least late February 2023 project nemesis Charlotte Hammond, a security researcher at IBM Security X-Force, said in a report published last week that it could steal information or use more powerful backdoors such as Cobalt Strike.
FIN7, also known as Carbanak and ITG14, is a prolific Russian-speaking cybercrime syndicate known for deploying additional malware and expanding monetization methods with its suite of custom malware.
A recent analysis by Google-owned Mandiant, SentinelOne, and PRODAFT implicates the group’s role as a precursor to Maze and Ryuk ransomware attacks, not to mention exposing connections to the Black Basta, DarkSide, REvil, and LockBit families. became clear.
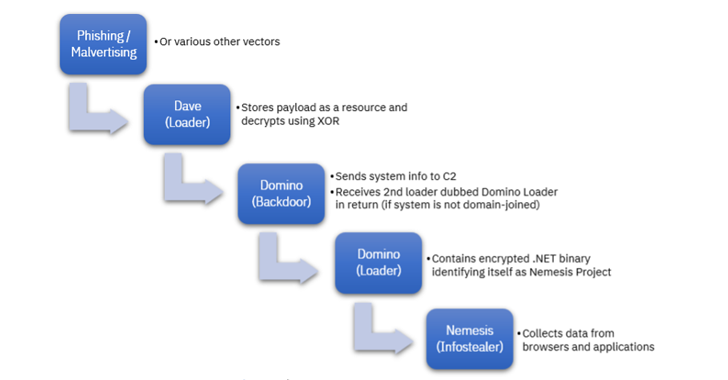
The latest wave of intrusions uncovered by IBM Security X-Force two months ago includes using Dave Loader, a crypter formerly attributed to the Conti group (aka Gold Blackburn, ITG23, or Wizard Spider) to Includes deploying a Domino backdoor.
A potential relationship between Domino and FIN7 comes from duplication of source code with the DICELOADER (aka Lizar or Tirion). This malware is designed to gather basic sensitive information and retrieve encrypted payloads from remote servers.
This next-stage artifact is a second loader, codenamed Domino Loader, possessing an encrypted .NET information stealer called Project Nemesis that can be used to access clipboards, Discord, web browsers, crypto wallets, VPNs The Service, and other apps may collect sensitive data.
“Domino has been active in the wild since at least October 2022, especially when Lizar observations began to decline,” Hammond noted, suggesting that attackers may be phasing out the latter. It shows that there is a
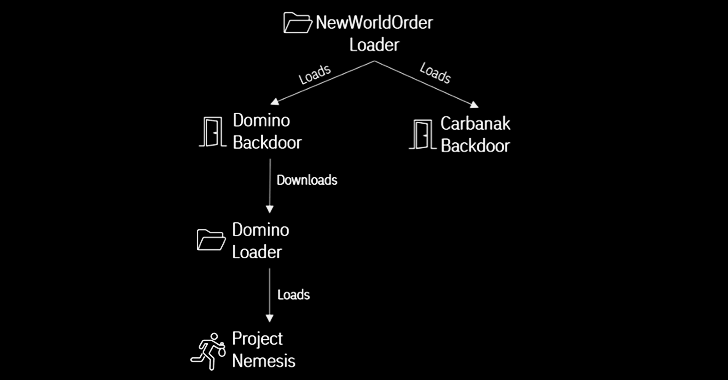
Another important link bridging Domino to FIN7 occurred in December 2022, leveraging another loader called NewWorldOrder Loader to deliver both Domino and Carbanak backdoors.
Master the Art of Dark Web Intelligence Gathering
Learn the art of extracting threat intelligence from the dark web – join us for this expert-led webinar!
Save my seat!
The Domino backdoor and loader (both 64-bit DLLs written in Visual C++) were allegedly used to install Project Nemesis since at least October 2022, before being used by a former Conti member earlier this year. I’m here.
The use of stealer malware by ransomware distributors is not without precedent. In November 2022, Microsoft revealed an intrusion staged by a threat actor known as DEV-0569. It leveraged the BATLOADER malware to deliver his Vidar and Cobalt Strike, the latter ultimately facilitating a human-operated ransomware attack distributing the Royal ransomware.
This increased the likelihood that information stealers would be deployed during low priority infections (such as personal computers) and Cobalt Strike would be offered to infections belonging to an Active Directory domain.
“The use of malware associated with multiple groups in a single campaign, such as Dave Loader, Domino Backdoor, and Project Nemesis Infostealer, not only highlights the complexity involved in tracking attackers, but also how , it also provides insight into who you work with,” concluded Hammond. .









