A new QBot malware campaign leverages hijacked business communications to trick unsuspecting victims into installing malware, new research from Kaspersky reveals.
The latest campaign, launched on April 4, 2023, primarily targets users in Germany, Argentina, Italy, Algeria, Spain, the United States, Russia, France, the United Kingdom, and Morocco.
QBot, also known as Qakbot or Pinkslipbot, is a banking Trojan known to have been active since at least 2007. Besides stealing passwords and cookies from web browsers, it also acts as a backdoor to inject next-stage payloads such as Cobalt Strike and ransomware.
Distributed via phishing campaigns, the malware has seen constant updates during its lifetime incorporating anti-VM, anti-debugging, and anti-sandboxing techniques to evade detection. It has also emerged as the most prevalent malware in March 2023, according to Check Point.
Explaining how QBot was distributed, Kaspersky researchers said, “Early on, it was distributed through compromised websites and pirated software. , and spam emails to potential victims.”
Email thread hijacking attacks are nothing new. This happens when cybercriminals interrupt existing business conversations or initiate new conversations based on information previously collected by compromised email accounts.
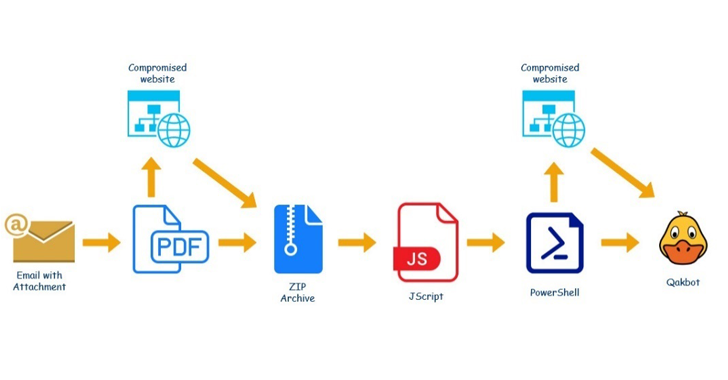
The goal is to trick the victim into opening a malicious link or malicious attachment (in this case, an enclosed PDF file disguised as a Microsoft Office 365 or Microsoft Azure alert).
Master the Art of Dark Web Intelligence Gathering
Learn the art of extracting threat intelligence from the dark web – join us for this expert-led webinar!
Save my seat!
An archive file is retrieved from the infected website when the document is opened. This archive file contains an obfuscated Windows Script File (.WSF). This script contains a PowerShell script that downloads a malicious DLL from a remote server. The downloaded DLL is QBot malware.
This finding led Elastic Security Labs to discover a multi-stage social engineering campaign using weaponized Microsoft Word documents to distribute Agent Tesla and XWorm using a custom .NET-based loader. It is due to









