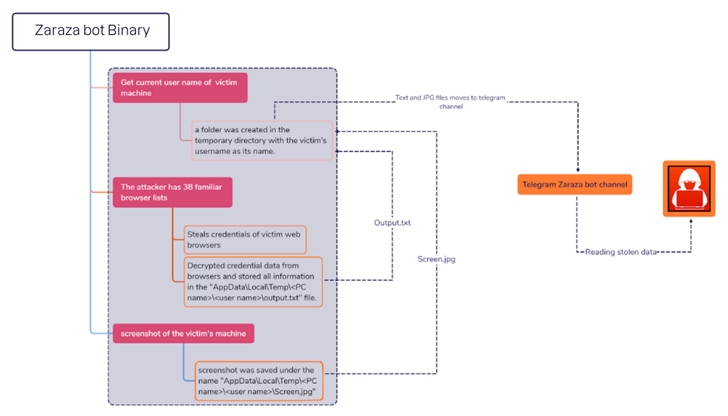
A new credential-stealing malware called Zarazabot It is marketed by Telegram while using the popular messaging service as command and control (C2).
“The Zaraza bot targets numerous web browsers and is actively distributed on the Russian Telegram hacker channel, which is popular with attackers,” cybersecurity firm Uptycs said in a report published last week.
“Once the malware infects a victim’s computer, it takes sensitive data and sends it to Telegram servers where the attacker has immediate access.”
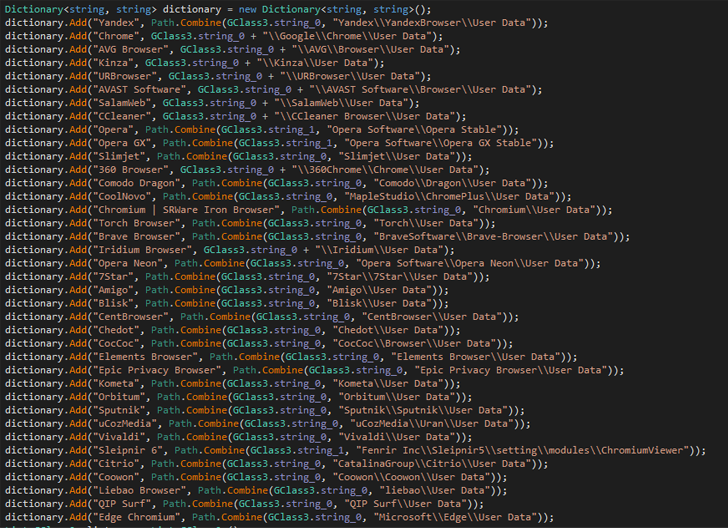
A 64-bit binary file compiled using C#, the Zaraza bot is designed to target up to 38 different web browsers including Google Chrome, Microsoft Edge, Opera, AVG Browser, Brave, Vivaldi and Yandex. It has been. It also has the ability to capture screenshots of active windows.
This is the latest example of malware that can obtain login credentials associated with online bank accounts, cryptocurrency wallets, email accounts, and other websites deemed valuable by operators.
Stolen credentials pose a serious risk, as they allow attackers to gain unauthorized access to victims’ accounts, as well as carry out identity theft and financial fraud.
Evidence gathered by Uptycs indicates that the Zaraza bot is offered as a commercial tool for subscriptions to other cybercriminals. It’s currently unclear how malware spreads, but information thieves have typically used several methods in the past, including malvertising and social engineering.
The findings come from eSentire’s Threat Response Unit (TRU) uncovering a GuLoader (aka CloudEyE) campaign targeting the financial sector via phishing emails. The campaign uses tax-themed lures to deliver Remote Access Trojans (RATs) like information thieves and his Remcos RAT.
Master the Art of Dark Web Intelligence Gathering
Learn the art of extracting threat intelligence from the dark web – join us for this expert-led webinar!
Save my seat!
This development has also led to the proliferation of malvertising and search engine poisoning techniques, prompting users looking for legitimate applications to download bogus installers containing stealer payloads, leading to the spread of an increasing number of malware families. Distributing.
In a new analysis, Russian cybersecurity firm Kaspersky found that Trojanized cracked software downloaded from BitTorrent or OneDrive was used as a conduit to install a cryptocurrency miner known as SilentCryptoMiner. Revealed that they are deploying CueMiner, a functional .NET-based downloader.
To reduce the risks posed by stealer malware, we recommend that users enable two-factor authentication (2FA) and apply software and operating system updates as they become available.









