A cybersecurity researcher said, “in2al5d p3in4er” (read: disabled printer) Used to deliver the Aurora information stealer malware.
“The in2al5d p3in4er loader is compiled with Embarcadero RAD Studio and uses advanced anti-VM (virtual machine) techniques to target endpoint workstations,” reports cybersecurity firm Morphisec shared with The Hacker News. said in
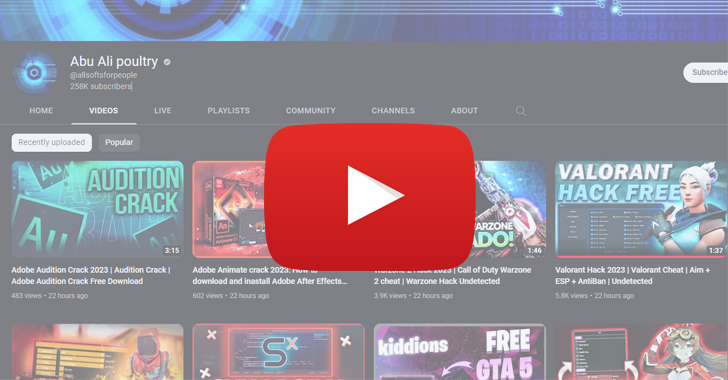
Aurora is a Go-based information-stealing program that has emerged in the threat landscape in late 2022. It is offered as commodity malware to other actors and distributed through YouTube videos and fake crack software download websites for SEO.
By clicking on the link in the YouTube video description, the victim is redirected to a decoy website and tricked into downloading malware under the guise of a seemingly legitimate utility.
The loader analyzed by Morphisec is designed to query the vendor IDs of the graphics cards installed on the system and compare them against a set of allowlisted vendor IDs (AMD, Intel, or NVIDIA). I’m here. If the values do not match, the loader exits.
The loader eventually decrypts the final payload and injects it into a legitimate process called ‘sihost.exe’ using a technique called process hollowing. Alternatively, some loader samples allocate memory, write the decrypted payload, and call it from there.
As security researchers Arnold Osipov and Michael Dereviashkin put it:

Another important aspect of the loader is that Embarcadero RAD Studio can be used to generate executables for multiple platforms, thereby evading detection.
“VirusTotal’s lowest detection rate is compiled using ‘BCC64.exe’, Embarcadero’s new Clang-based C++ compiler,” said the Israeli cybersecurity firm, which uses sandboxes and virtual machines to I pointed out the ability to dodge.
“This compiler uses different code bases such as the ‘standard library’ (Dinkumware) and the ‘runtime library’ (compiler-rt) to generate optimized code that changes entry points and execution flow. This breaks security vendor indicators such as signatures. It consists of “malicious/suspicious code blocks”. “
Master the Art of Dark Web Intelligence Gathering
Learn the art of extracting threat intelligence from the dark web – join us for this expert-led webinar!
Save my seat!
In a nutshell, our findings show that the threat actors behind in2al5d p3in4er leveraged social engineering techniques to use YouTube as a malware distribution channel to lure viewers to compelling fake websites. Indicates a high-impact campaign to distribute stealer malware.
This development is due to Intel 471’s discovery of another malware loader, AresLoader. AresLoader sells for $300/month as a service where criminals use binder tools to push information thieves disguised as common software. Loader is suspected to have been developed by a group associated with hacktivism in Russia.
Notable malware families that have used AresLoader to spread since January 2023 include Aurora Stealer, Laplas Clipper, Lumma Stealer, Stealc, and SystemBC.











