
Cyber spy actor tracked as blind eagle Linked to a new multi-stage attack chain that deploys the NjRAT remote access Trojan on compromised systems.
“The group is known to use a variety of advanced attack techniques, including custom malware, social engineering tactics, and spear-phishing attacks,” ThreatMon said in a Tuesday report.
Blind Eagle, also known as APT-C-36, is a suspected Spanish-speaking group that primarily attacks private and public sector organizations in Colombia. Attacks orchestrated by this group also target Ecuador, Chile and Spain.
Infection chains documented by Check Point and BlackBerry earlier this year reveal spear-phishing lures used to deliver commodity malware families such as BitRAT, AsyncRAT, and in-memory Python loaders capable of launching Meterpreter payloads became.
The latest discovery from ThreatMon involves using a JavaScript downloader to run a PowerShell script hosted on the Discord CDN. This script drops another PowerShell script and a Windows batch file and saves the VBScript file to the Windows Startup folder for persistence.
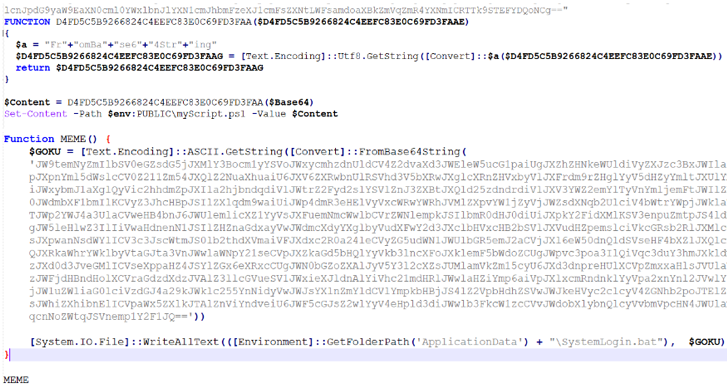
Then the VBScript code is executed to launch the batch file. It then deobfuscates and executes the PowerShell script previously delivered with it. The final step is to run njRAT using a PowerShell script.
“njRAT, also known as Bladabindi, is a remote access tool (RAT) with a user interface or Trojan horse that allows program owners to control end-user computers,” said the cybersecurity firm. said.









