State-backed actor associated with the infamous North Korea known as Lazarus Group attributed to a new campaign aimed at Linux users.
An attack is a piece of persistent, long-running activity tracked by that name. operation dream jobESET says in a new report published today.
This finding is significant as it is the first public example of an attacker using Linux malware as part of a social engineering scheme.
Operation Dream Job, also known as Death Note or NukeSped, refers to multiple waves of attacks. The group uses fraudulent job postings as lures to trick unsuspecting targets into downloading malware. It also shows overlap with two other of his Lazarus clusters known as Operation In(ter)ception and Operation North Star.
The attack chain discovered by ESET allegedly delivers fake HSBC jobs as decoys in ZIP archive files and is used to launch a Linux backdoor named SimplexTea distributed via OpenDrive cloud storage accounts. It makes no difference.
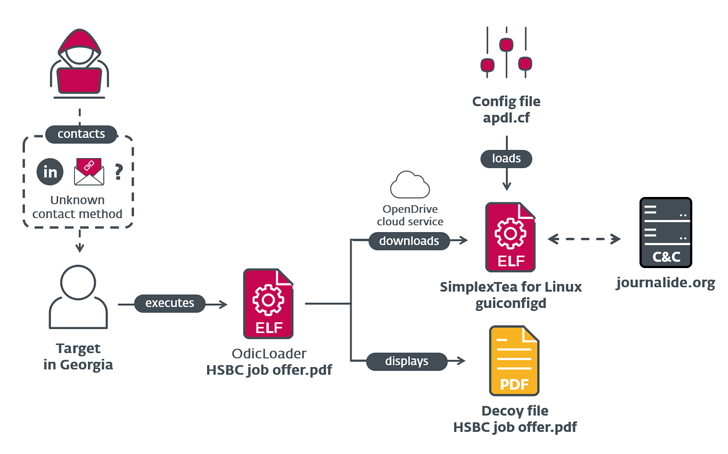
The exact method used to distribute the ZIP file is unknown, but it is suspected to be spear phishing or a LinkedIn direct message. This backdoor, written in C++, is similar to his BADCALL, a Windows Trojan previously attributed to this group.
Additionally, ESET says it has identified commonalities between the artifacts used in the Dream Job campaign and those discovered as part of a supply chain attack against VoIP software developer 3CX that was uncovered last month. said.
Defending with Deception: Driving Zero Trust Security
See how Deception can detect advanced threats, stop lateral movement, and strengthen your Zero Trust strategy. Join us for an insightful webinar!
Save my seat!
This also includes the command and control (C2) domain ‘journalide’.[.]org” was listed as one of four C2 servers used by malware families detected within the 3CX environment.
It indicates that preparations for a supply chain attack have been underway since December 2022, when some components were committed to the GitHub code hosting platform.
The findings not only strengthen the existing link between the Lazarus Group and the 3CX breach, but also show the actors’ continued success in staging supply chain attacks in 2020 and beyond.









