Cybersecurity researchers have discovered a patched zero-day vulnerability in Google Cloud Platform (GCP) that allows attackers to hide irremovable malicious applications inside a victim’s Google account. clarified the details.
dubbing ghost token According to Israeli cybersecurity startup Astrix Security, the shortcoming affects all Google accounts, including Workspace accounts for enterprises. It was discovered on June 19, 2022 and reported to Google. The company rolled out a global patch on April 7, 2023, more than nine months after he.
“Vulnerability […] By transforming an already-approved third-party application into a malicious Trojan app, the attacker gains permanent and irremovable access to the victim’s Google account and uses the victim’s personal We can publish data forever,” Astrix said in the report.
Simply put, this vulnerability allows attackers to hide malicious apps from the application management page of the victim’s Google account, effectively preventing users from revoking access.
This is accomplished by deleting the GCP project associated with the authorized OAuth application, leaving it in a “pending deletion” state. An attacker with this capability could restore the project, unhide the rogue app, use the access token to retrieve the victim’s data, and then unhide it again.
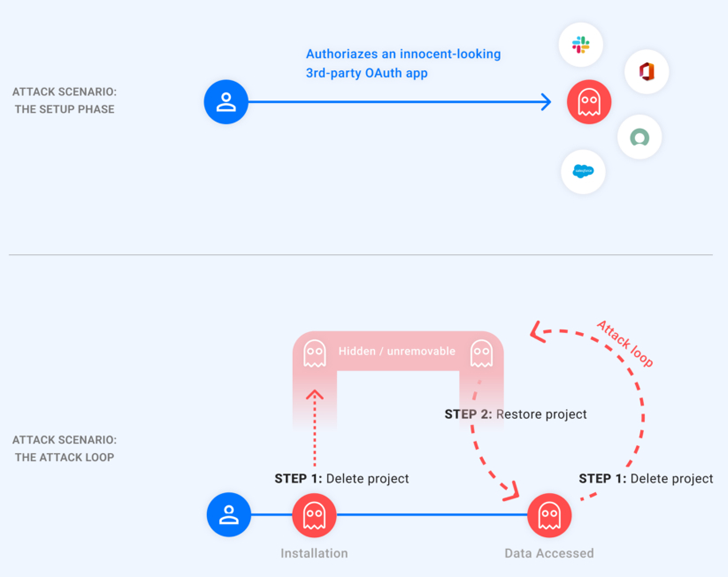
“In other words, the attacker holds a ‘ghost’ token in the victim’s account,” said Astrix.
The type of data you can access depends on the permissions granted to your app. Attackers can abuse this privilege to delete files from Google Drive, compose emails on behalf of victims to carry out social engineering attacks, track locations, or steal sensitive data from Google. You can Calendars, photos, drives.
“By installing a seemingly harmless app from the Google Marketplace or one of the many productivity tools available online, victims unknowingly allow access to such malicious applications. We could do that,” Astrix added.
Zero Trust + Deception: Learn How to Outsmart Attackers!
See how Deception can detect advanced threats, stop lateral movement, and strengthen your Zero Trust strategy. Join us for an insightful webinar!
Save my seat!
“Once a malicious app is approved, an attacker who exploits the vulnerability can bypass Google’s ‘apps with account access’ control feature. This is the only place a Google user can view third-party her apps connected to her account. ”
Our patch addresses the issue by showing apps pending removal on the third-party access page, allowing users to revoke the permissions granted to such apps.
With this development, Google Cloud discovered a privilege escalation flaw in its cloud asset inventory API, known as Asset Key Thief, that could be exploited to steal the private keys of user-managed service accounts and access valuable data. This is due to the modification. The issue was discovered by SADA in February of this year and patched by the tech giant on March 14, 2023.
The findings come just over a month after cloud incident response firm Mitiga revealed that attackers could use “insufficient” forensic visibility into GCP to exfiltrate sensitive data. Done.









