
The supply chain attack targeting 3CX is the result of a previous supply chain compromise involving another company and represents a new level of sophistication for the North Korean threat actor.
Mandiant, owned by Google, tracks attack events by name. UNC4736said the incident was the first to see “a software supply chain attack lead to another software supply chain attack.”
The matryoshka doll-style cascading attack against 3CX was first revealed on March 29, 2023. At this time, Windows and macOS versions of its communications software were trojanized, and a C/C++-based data miner named ICONIC Stealer launched a downloader, SUDDENICON, using an icon file hosted on GitHub to download the stealer. I extracted the server containing.
“The malicious application then attempts to steal sensitive information from the victim user’s web browser,” said the US Cybersecurity and Infrastructure Security Agency (CISA) in its analysis of the malware. “Specifically targets Chrome, Edge, Brave, or Firefox browsers.”
Some attacks targeting cryptocurrency companies also required the deployment of a next-stage backdoor called Gopuram, which could execute additional commands and interact with the victim’s file system.
Mandiant’s investigation into the chain of events revealed that Patient 0 had a malicious version of a now-discontinued software provided by fintech firm Trading Technologies that a 3CX employee downloaded onto his personal computer. One thing became clear.
The first intrusion vector has been described as “malware-laden software packages distributed via previous software supply chain breaches, starting with X_TRADER’s compromised installer.”
The malicious installer contained a setup binary that dropped two trojanized DLLs and a harmless executable.
The attack chain then leveraged open source tools such as SIGFLIP and DAVESHELL to finally extract and execute VEILEDSIGNAL. VEILEDSIGNAL is a multi-stage modular backdoor written in C that can send data, execute shellcode, and terminate itself.
The initial compromise of an employee’s PC using VEILEDSIGNAL allowed the attacker to obtain the individual’s corporate credentials. Twice later, stolen credentials were used to gain initial unauthorized access to the network via her VPN.
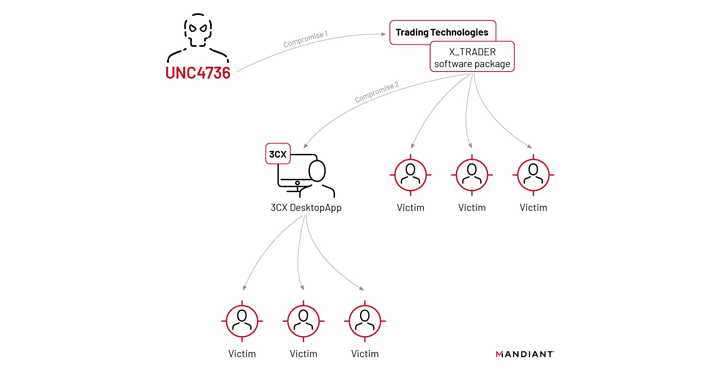
Mandiant identified tactical similarities between the compromised X_TRADER and 3CXDesktopApp apps, and found that the attackers then moved laterally within the 3CX environment and compromised Windows and macOS build environments. Did.
“In the Windows build environment, the attackers deployed the TAXHAUL launcher and COLDCAT downloader, which survived by sideloading DLLs through the IKEEXT service and ran with LocalSystem privileges,” said Mandiant. says. “A macOS build server was compromised with his POOLRAT backdoor that uses Launch Daemons as a persistence mechanism.”
POOLRAT, formerly classified as SIMPLESEA by the threat intelligence firm, is a C/C++ macOS implant that can gather basic system information and execute arbitrary commands, including performing file operations.
UNC4736 is a suspected threat group associated with North Korea, bolstered by ESET’s discovery of overlapping command and control (C2) domains (Journal[.]org) has been used in supply chain attacks and in a campaign called Operation Dream Job by Lazarus Group.
Evidence collected by Mandiant shows this group shares commonalities with another set of intrusions tracked as Operation AppleJeus. This intrusion group has a track record of carrying out financially motivated attacks.
Zero Trust + Deception: Learn How to Outsmart Attackers!
See how Deception can detect advanced threats, stop lateral movement, and strengthen your Zero Trust strategy. Join us for an insightful webinar!
Save my seat!
Additionally, the compromise of Trading Technologies’ website, in early February 2022, weaponized a then-zero-day vulnerability in Google Chrome (CVE-2022-0609), resulting in a multi-step attack that caused an unknown service to be delivered. It is said to have occurred by activating the infection chain. Payload to site visitors.
“Site www.tradingtechnologies[.]com was compromised and hosted a hidden IFRAME to exploit visitors, just two months before it was known that the site was delivering a trojanized X_TRADER software package.” Mandiant explains.
Another link that ties it to AppleJeus is that the attackers have previously used older versions of POOLRAT as part of a long-running campaign to spread booby-trapped trading applications like CoinGoTrade to facilitate cryptocurrency theft. is.
The overall scale of the campaign remains unknown, and it is currently unclear whether the compromised X_TRADER software was used by other companies. The platform was supposedly discontinued in April 2020, but it was still available for download on the site in 2022.
Update shared on April 20, 2023, 3CX hardens its systems and promotes nested software-in-software by enhancing product security and incorporating tools to ensure software integrity. It said it was taking steps to minimize the risk of supply chain attacks. Establish a new division for network operations and security.
“A cascading software supply chain breach involves a North Korean operator creatively exploiting network access to develop and distribute malware to move between target networks while performing operations in the interest of North Korea. It shows that you can move,” said Mandiant.









