A new “all-in-one” stealer malware named Evil Extractor (also known as Evil Extractor) is sold to other attackers to steal data and files from Windows systems.
Fortinet FortiGuard Labs researcher Cara Lin said: “Environment checks and anti-VM functionality are also included. Its primary purpose appears to be to steal browser data and information from compromised endpoints and upload them to the attacker’s girlfriend’s FTP server.”
EvilExtractor has observed a spike in attacks distributing malware in March 2023, with the majority of victims living in Europe and the United States. as an information thief.
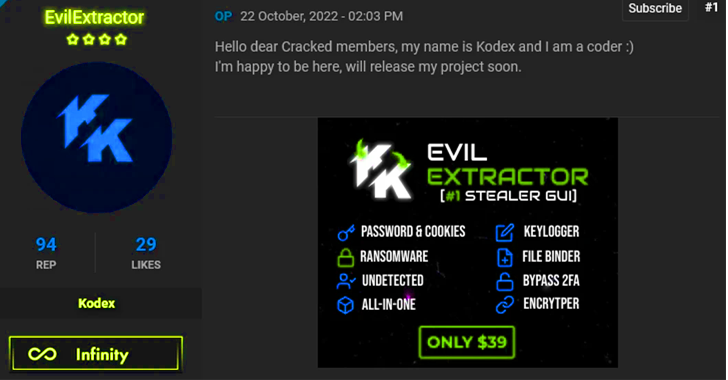
Since October 22, 2022, it has been sold by an actor named Kodex on cybercrime forums such as Cracked. It is continuously updated and packed into various modules to siphon system metadata, passwords and cookies from various web browsers, log keystrokes and even act as ransomware with encryption. A file on the target system.
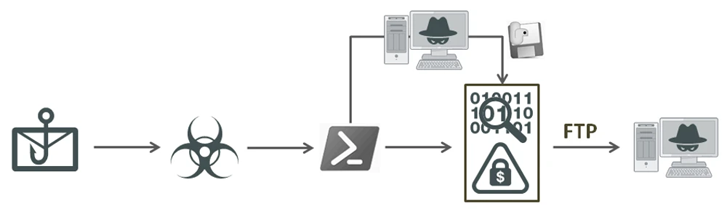
This malware was also allegedly used as part of a phishing email campaign that the company detected on March 30, 2023. This email lures the recipient into launching an executable disguised as a PDF document under the pretext of “verifying account details”. “
The “Account_Info.exe” binary is an obfuscated Python program designed to launch a .NET loader that launches EvilExtractor using a Base64-encoded PowerShell script. In addition to collecting files, this malware can also activate your webcam and capture screenshots.
“EvilExtractor is used as a comprehensive information stealer with multiple malicious functions including ransomware,” said Lin. “That his PowerShell script could escape detection by the .NET loader or his PyArmor.In a very short time the developer has updated several features and improved stability. ”
This finding details a malvertising and SEO poisoning campaign used by the Secureworks Counter Threat Unit (CTU) to deliver the Bumblebee malware loader via trojanized installers of legitimate software. that made it clear.
First documented a year ago by Google’s Threat Analysis Group and Proofpoint, Bumbleebee is a modular loader that spreads primarily through phishing techniques. It is suspected to have been developed by the actors involved in the Conti ransomware operation as an alternative to BazarLoader.
Zero Trust + Deception: Learn How to Outsmart Attackers!
See how Deception can detect advanced threats, stop lateral movement, and strengthen your Zero Trust strategy. Join us for an insightful webinar!
Save my seat!
Users searching for popular tools such as ChatGPT, Cisco AnyConnect, Citrix Workspace, and Zoom can be redirected to rogue websites hosting tainted installers using SEO poisoning and malicious ads. , has surged in recent months after Microsoft began blocking macros by default from downloaded Office files. from the internet.
In one incident described by a cybersecurity firm, attackers used the Bumblebee malware to gain an entry point and three hours later moved laterally to launch Cobalt Strike and legitimate remote access software such as AnyDesk and Dameware. was expanded. The attack was eventually interrupted before proceeding to the final ransomware stage.
“To mitigate this and similar threats, organizations should ensure that software installers and updates are only downloaded from known and trusted websites,” Secureworks said. “Users should not have permission to install software and run scripts on their computers.”









