The attackers employ what they call a previously undocumented “defense evasion tool.” Orchill It is designed to defeat endpoint detection and response (EDR) software with a Bring Your Own Vulnerable Driver (BYOVD) attack.
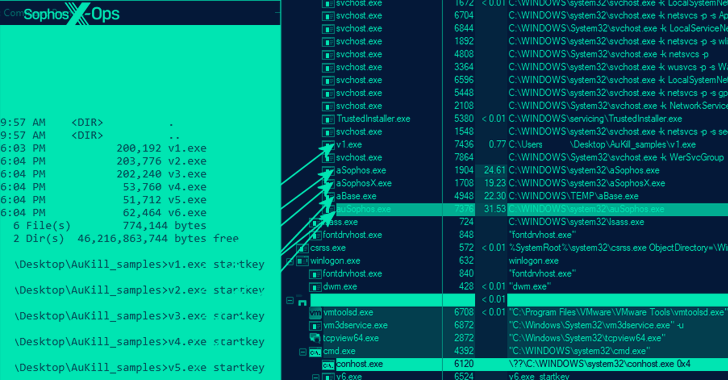
“The AuKill tool exploits outdated drivers used by version 16.32 of the Microsoft utility Process Explorer to disable EDR processes before deploying backdoors or ransomware on target systems,” Sophos research author Andreas Klopsch said in the last published report. week.
Incidents analyzed by a cybersecurity firm show that since the beginning of 2023, AuKill has been used to deploy various ransomware strains such as Medusa Locker and LockBit. To date, six different versions of his malware have been identified. The oldest AuKill sample has a compile timestamp of November 2022.
BYOVD techniques allow threat actors to exploit legitimate but outdated exploitable drivers signed by Microsoft (or use stolen or leaked certificates) to elevate privileges and turn off security mechanisms. depends on what you do.
A key Windows safeguard known as Driver Signature Enforcement that uses genuine and exploitable drivers to ensure that kernel-mode drivers are signed by a valid code signing authority before they are allowed to run. can be bypassed.
“The AuKill tool requires administrative privileges to function, which the attacker cannot give,” said the Sophos researcher. “Attackers using AuKill took advantage of existing privileges during the attack and gained privileges through other means.”
This isn’t the first time the Microsoft-signed Process Explorer driver has been weaponized in an attack. In November 2022, Sophos also detailed his LockBit affiliate’s use of an open-source tool called Backstab. The tool was exploiting outdated drivers to terminate protected antimalware processes.
Then, earlier this year, a malvertising campaign was discovered leveraging the same driver to distribute a .NET loader named MalVirt to deploy FormBook information-stealing malware.
This development reveals that a poorly managed MS-SQL server has been weaponized to install Trigona ransomware that duplicates another strain called CryLock, AhnLab Security Emergency Response Center (ASEC) reveals. Occurs when
Actors of the Play ransomware (aka PlayCrypt) also use a custom data collection tool that allows them to enumerate all users and computers on a compromised network and copy files from the Volume Shadow Copy Service (VSS). This is also followed by the survey result that it was observed that
Grixba, a .NET-based information stealer, is designed to scan machines for security programs, backup software, and remote administration tools, exfiltrate the collected data in the form of CSV files, and compress them into ZIP archives. I’m here.
Also used by the cybercrime gang tracked by Symantec as Balloonfly is a VSS copy tool written in .NET. This tool leverages the AlphaVSS framework to list the files and folders in the VSS snapshot and copy them to the destination directory before encrypting them.
Zero Trust + Deception: Learn How to Outsmart Attackers!
See how Deception can detect advanced threats, stop lateral movement, and strengthen your Zero Trust strategy. Join us for an insightful webinar!
Save my seat!
Not only does Play ransomware utilize intermittent encryption to speed up the process, it is also noteworthy that it does not operate on a Ransomware as a Service (RaaS) model. Evidence collected so far indicates that Balloonfly carried out ransomware attacks and developed the malware itself.
Grixba and the VSS Copying Tool are the latest in a long list of proprietary tools used by ransomware attackers to gain more control over their operations, including Exmatter, Exbyte, and PowerShell-based scripts, while persisting. Add a layer of complexity for Infiltrate compromised environments and evade detection.
Another technique increasingly employed by financially motivated groups is to use the Go programming language to develop cross-platform malware to resist analysis and reverse engineering efforts.
In fact, a report from Cyble last week documented a new GoLang ransomware called CrossLock. This ransomware employs double extortion techniques to increase the likelihood of payment from victims and takes steps to avoid Windows (ETW) event tracing.
“This feature allows malware to evade detection by security systems that rely on event logs,” Cyble said. “CrossLock ransomware takes several actions to increase the effectiveness of the attack while reducing the chances of data recovery.”











