Print management software provider PaperCut cites two vulnerability reports from cybersecurity firm Trend Micro, citing “evidence that suggests unpatched servers are being exploited in the wild.” said.
“PaperCut has conducted an analysis of all customer reports and the first signature of suspicious activity on customer servers that may be related to this vulnerability was posted on Apr 14 01:29 AEST / Apr 15:29 UTC on the 13th,” he added.
This update adds the U.S. Cybersecurity and Infrastructure Security Agency (CISA) a critical flaw (CVE-2023-27350, CVSS This is done when adding the score – 9.8).
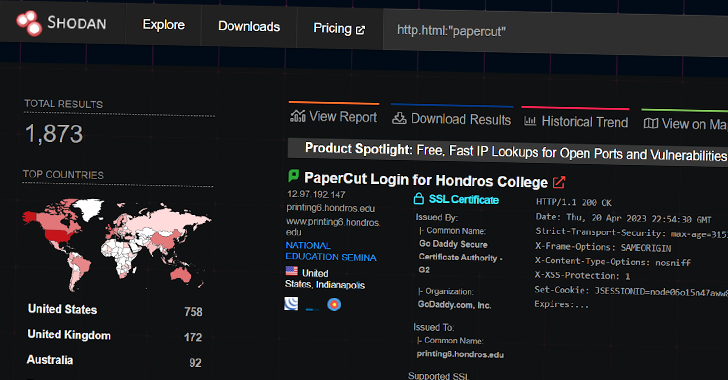
Huntress, a cybersecurity firm that discovered about 1,800 publicly available PaperCut servers, discovered that PowerShell commands were generated from the PaperCut software to install remote management and maintenance (RMM) software such as Atera and Syncro to target infected hosts. It says above that it confirmed to have persistent access and code execution.
Additional infrastructure analysis revealed the domain hosting the tool – windowservicecemter[.]com – was registered on April 12, 2023 and also hosted malware like TrueBot, but the company said it did not directly detect the deployment of the downloader.
TrueBot is believed to have been attributed to a Russian criminal syndicate known as Silence. It has historical ties to Evil Corp and its duplicate cluster TA505, the latter of which has facilitated his Cl0p ransomware distribution in the past.
Researchers at Huntress said, “Although the ultimate purpose of the current activity using PaperCut’s software is unknown, these links (albeit contextual) to known ransomware entities are concerning. ‘ said.
Zero Trust + Deception: Learn How to Outsmart Attackers!
See how Deception can detect advanced threats, stop lateral movement, and strengthen your Zero Trust strategy. Join us for an insightful webinar!
Save my seat!
“Potentially, the access gained by the PaperCut exploit could be used as a stepping stone leading to subsequent movement within the victim’s network and ultimately the deployment of the ransomware.”
Users should install fixed versions of PaperCut MF and NG (20.1.7, 21.2.11, and 22.0.9) to mitigate whether the server is “available for external or internal connections” We recommend that you upgrade to as soon as possible. potential risk.
Customers who cannot upgrade to the security patch are encouraged to lock down network access to their servers by blocking all inbound traffic from external IPs and restricting IP addresses to only IP addresses belonging to verified site servers. It is recommended.









