Iranian nation-state threat actors have been linked to a new wave of phishing attacks targeting Israel.This is designed to deploy an updated version of the backdoor helpless.
Cybersecurity firm Check Point tracks activity clusters under the handles of mythical creatures Educated ManticoreAPT35, Charming Kitten, Cobalt Illusion, ITG18, Mint Sandstorm (formerly Phosphorus), TA453, and the hacking crew known as Yellow Garuda show “strong overlap”.
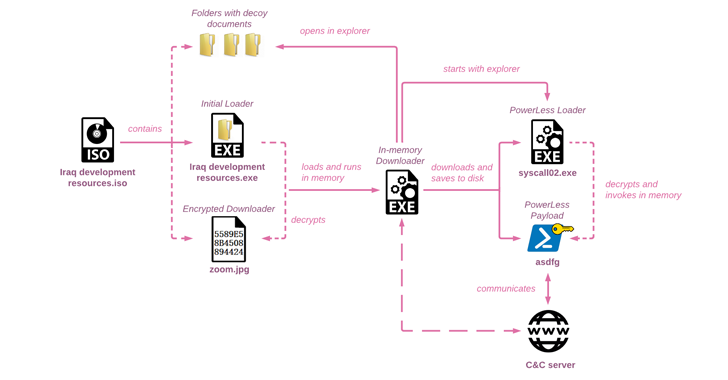
“Like many other threat actors, Educated Manticore has taken advantage of recent trends and started using ISO images and possibly other archive files to initiate the infection chain,” the Israeli company said today. stated in the technical report issued.
Active since at least 2011, APT35 leverages fake social media personas, spear phishing techniques, and N-day vulnerabilities in Internet-facing applications to gain initial access and launch various attacks, including ransomware. It has posed a wide range of targets by dropping nasty payloads.
This development shows that attackers are continually refining and rebuilding their malware arsenal to expand their capabilities and resist analysis efforts while employing enhanced methods to evade detection. I’m here.
The attack chain documented by Check Point begins with an ISO disk image file that utilizes an Iraqi-themed lure to drop a custom in-memory downloader that ultimately launches the PowerLess implant.
The ISO file serves as a conduit for viewing decoy documents written in Arabic, English, and Hebrew, and academic content about Iraq from a legitimate non-profit organization called the Arab Science and Technology Foundation (ASTF). Claims to be featured. The research community may have been the target of the campaign.
The PowerLess backdoor spotted by Cybereason in February 2022 has the ability to steal data, take screenshots, record audio, and record keystrokes from web browsers and apps like Telegram. .
“Although the new PowerLess payload is similar, the loading mechanism is much improved and employs techniques rarely seen in practice, such as using assembly code and mixed-mode .NET binary files. ,” said Check Point.
“Powerless [command-and-control] Communication to the server is Base64 encoded and encrypted after obtaining the key from the server. To mislead the researchers, the attacker actively prepends her three random characters to the encoded blob. ”
Zero Trust + Deception: Learn How to Outsmart Attackers!
See how Deception can detect advanced threats, stop lateral movement, and strengthen your Zero Trust strategy. Join us for an insightful webinar!
Save my seat!
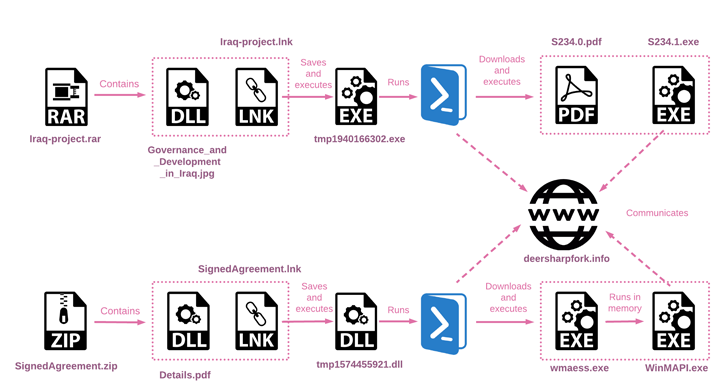
The cybersecurity firm said it also discovered two other archived files used as part of another set of intrusions that overlapped with the aforementioned attack sequence by using the same Iraqi-themed PDF files.
Further analysis revealed that the infection chain stemming from these two archive files led to execution of a PowerShell script designed to download and execute two files from a remote server.
Check Point said:
“Because it is an updated version of previously reported malware, […] It is important to note that this is only the early stages of infection and a significant portion of post-infection activity has yet to be seen in action. ”









