Chinese nation-state group called alloy taurus uses a Linux version of a backdoor called PingPull and a new undocumented tool codenamed Sword2033.
This is according to Palo Alto Networks Unit 42 research, which uncovered recent malicious cyber activity targeting South Africa and Nepal.
Alloy Taurus is a constellation-themed moniker assigned to a threat actor known for attacks targeting telecommunications companies since at least 2012. It is also tracked by Microsoft as Granite Typhoon (formerly Gallium).
Last month, the adversary was attributed to a campaign called Tainted Love, which targeted telecom providers in the Middle East as part of a wider operation called Soft Cell.
Also, recent cyber espionage attacks staged by Alloy Taurus have broadened their footprint to victims including financial institutions and government agencies.
First documented by Unit 42 in June 2022, PingPull is a remote access Trojan that uses the Internet Control Message Protocol (ICMP) for command and control (C2) communication.
Linux-based malware has the same functions as the Windows version, and can perform file operations or execute arbitrary commands by sending one capital letter between A and K and M from the C2 server. You can
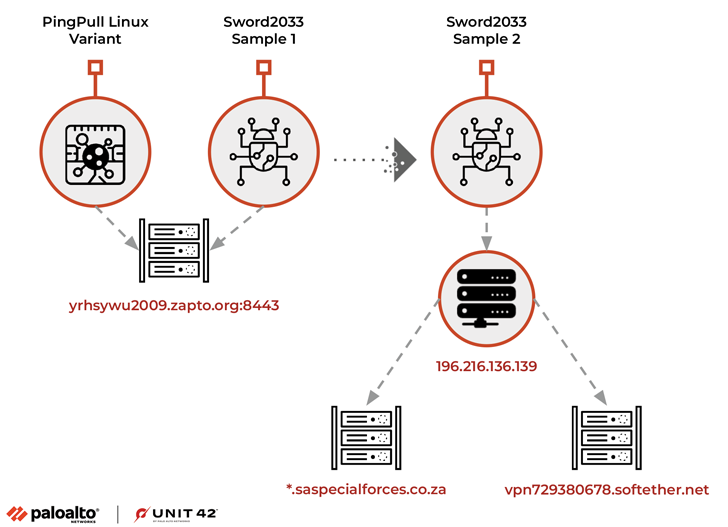
“When executed, this sample will be configured to communicate with the domain yrhsywu2009.zapto.[.]Unit 42 states, “We access org through port 8443 on C2. We use the statically linked OpenSSL (OpenSSL 0.9.8e) library to interact with the domain over HTTPS.” increase.
Interestingly, PingPull’s analysis of the C2 instructions mirrors that of China Chopper, a web shell widely used by Chinese threat actors, allowing threat actors to repurpose existing source code to build custom tools. It suggests that you are thinking about it.
Closer inspection of the aforementioned domains also revealed the presence of other ELF artifacts, such as Sword2033. This artifact supports three basic functions including uploading and extracting files and executing commands.
Zero Trust + Deception: Learn How to Outsmart Attackers!
See how Deception can detect advanced threats, stop lateral movement, and strengthen your Zero Trust strategy. Join us for an insightful webinar!
Save my seat!
Malware links to the Alloy Taurus are to IP addresses previously identified as active indicators of compromise (ICs) associated with previous campaigns targeting companies operating in Southeast Asia, Europe, and Africa. It comes from the fact that the domain is resolved.
South Africa was targeted against the backdrop of hosting a 10-day naval exercise jointly with Russia and China earlier this year, according to the cybersecurity firm.
Unit 42 said: “Alloy Taurus remains a threat to telecommunications, financial and government institutions in Southeast Asia, Europe and Africa.
“The identification of the Linux variant of the PingPull malware and the recent use of the Sword2033 backdoor suggest that this group continues to evolve its operations to aid espionage.”











