Advanced Persistent Threat (APT) group called dodging panda has been observed targeting international non-governmental organizations (NGOs) in mainland China, using malware distributed through legitimate application update channels such as Tencent QQ.
The attack chain is designed to distribute the MgBot malware Windows installer, ESET security researcher Facundo Muñoz said in a new report published today. This activity he started in November 2020 and will continue throughout 2021.
Evasive Panda, also known as Bronze Highland and Daggerfly, is a Chinese-speaking APT group that has since at least launched a series of cyber attacks targeting various entities in China, Hong Kong, and other countries in East and South Asia. It is believed to have been caused by a spy attack. Late December 2012.
A distinctive feature of this group is the use of a custom MgBot modular malware framework. This framework can receive additional components on the fly to extend its intelligence gathering capabilities.
Notable features of this malware include file stealing, keystroke logging, clipboard data collection, audio stream recording, and credential stealing from web browsers.
ESET, which discovered the campaign after deploying the MgBot backdoor installer using a legitimate Chinese application in January 2022, said the targeted users resided in the provinces of Gansu, Guangdong and Jiangsu. said he was a member of an unknown international NGO.
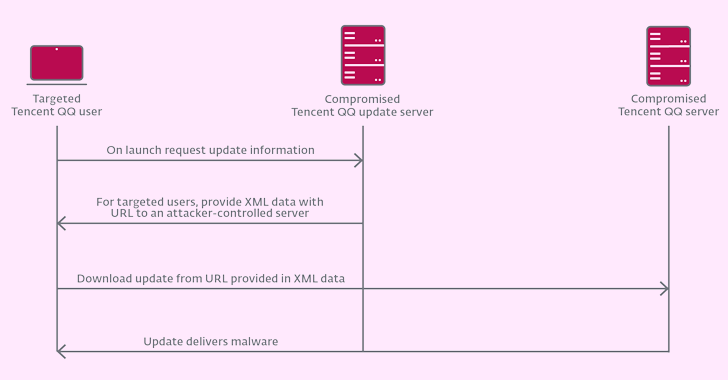
The trojanized application is Tencent QQ Windows Client Software Updater (“QQUrlMgr.exe”) hosted on the domain “update.browser.qq”.[.]com.” It is not immediately clear how the attacker distributed the implant through legitimate updates.

But it could be one of two scenarios, a supply chain compromise of Tencent QQ’s update servers, or an adversary (AitM) attack case detailed by Kaspersky in June 2022 involving a Chinese hacking crew called LuoYu. is shown. .
In recent years, many software supply chain attacks have been orchestrated by groups of nations in Russia, China, and North Korea. These attackers have not lost their ability to quickly acquire a large malicious footprint. These attackers are increasingly targeting the IT supply chain to compromise corporate environments.
Zero Trust + Deception: Learn How to Outsmart Attackers!
See how Deception can detect advanced threats, stop lateral movement, and strengthen your Zero Trust strategy. Join us for an insightful webinar!
Save my seat!
“If either LuoYu or Evasive Panda attackers were able to compromise vulnerable devices such as routers and gateways, AitM-style interception would be possible,” Muñoz elaborated.
“When accessing ISP backbone infrastructure through legal or illegal means, Evasive Panda can intercept and respond to update requests made over HTTP, or even modify packets.”
This is significant because the findings came less than a week after Broadcom-owned Symantec launched a detailed attack against an African telecom service provider using the MgBot malware framework.











