
The maintainers of the Apache Superset open source data visualization software have released a fix to plug in an insecure default configuration that could lead to remote code execution.
Vulnerabilities tracked as CVE-2023-27524 (CVSS score: 8.9), affecting versions up to 2.0.1, and changing the default SECRET_KEY that attackers can exploit to authenticate and access unauthenticated resources in Internet-facing installations. related to use.
Naveen Sunkavally, chief architect of Horizon3.ai, describes the issue as “a dangerous default configuration in the Apache superset that allows unauthenticated attackers to remotely execute code and harvest credentials. and allows data to be compromised.”
Note that this flaw does not affect superset instances that change the default value of the SECRET_KEY configuration to a more cryptographically secure random string.
1,288 publicly accessible cybersecurity firms discovered that SECRET_KEY defaulted to “\x02\x01thisismysecretkey\x01\x02\\e\\y\\y\\h” during installation 918 of those servers were using default settings in October 2021.
An attacker who knows the private key can forge the session cookie to sign into these servers as an administrator and gain control of the system.
On January 11, 2022, the project maintainer attempted to fix the issue by rotating the value of SECRET_KEY to “CHANGE_ME_TO_A_COMPLEX_RANDOM_SECRET” in Python code and following user instructions to override it.
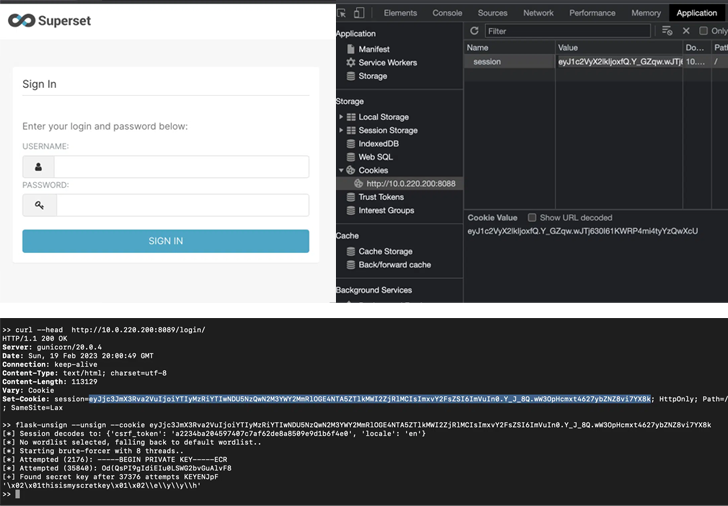
Horizon3.ai further states that they found two additional SECRET_KEY configurations assigned default values of “USE_YOUR_OWN_SECURE_RANDOM_KEY” and “thisISaSECRET_1234”.
An expanded search conducted in February 2023 using these four keys found 3,176 instances, of which 2,124 used one of the default keys. Those affected include large companies, small businesses, government agencies, and universities.
Following a second responsible disclosure to the Apache security team, a new update (version 2.1) was released on April 5, 2023. This closes a security hole by preventing the server from completely starting if it is configured with the default his SECRET_KEY.
Zero Trust + Deception: Learn How to Outsmart Attackers!
See how Deception can detect advanced threats, stop lateral movement, and strengthen your Zero Trust strategy. Join us for an insightful webinar!
Save my seat!
“It’s still possible to run a superset with the default SECRET_KEY when installed via a Docker-compose file or a helm template, so this fix is unreliable,” said Sunkavally.
“The docker-compose file contains a new default SECRET_KEY of TEST_NON_DEV_SECRET which I suspect some users unknowingly run a superset of. Some configs have default credentials for the admin user The information admin/admin is also set.”
Horizon3.ai has also made available a Python script that can be used to determine if a superset instance is susceptible to this vulnerability.
“It’s generally accepted that users don’t read documentation, and applications should be designed to force users down a path that has no choice but to be safe by default,” said Sunkavally. I’m wrapping up. “The best approach is to deprive users of choice and force them to act deliberately because they are deliberately insecure.”











