South Korean educational institutions, construction institutions, diplomatic institutions, and political institutions are under renewed attacks by China-linked threat actors. tonto team.
In a report published this week, the AhnLab Security Emergency Response Center (ASEC) said, “In recent cases, the group used files associated with anti-malware products to ultimately carry out malicious attacks. has become clear,” he said.
The Tonto Team has been around since at least 2009 and has a proven track record of targeting different sectors in Asia and Eastern Europe. Earlier this year, the group was attributed to a failed phishing attack against cybersecurity firm Group-IB.
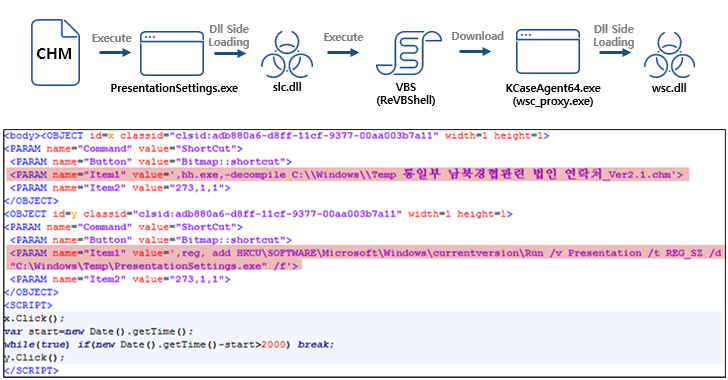
The attack sequence discovered by ASEC involves executing a binary file, sideloading a malicious DLL file (slc.dll) and launching ReVBShell, an open source VBScript backdoor Microsoft Compiled HTML Help (.CHM) Start with a file. Another Chinese threat actor called Tick.
It then uses ReVBShell to download a second executable, a legitimate Avast software configuration file (wsc_proxy.exe), sideload a second malicious DLL (wsc.dll), and finally Bisonal. Deploys a remote access Trojan.
“The Tonto team is constantly evolving through a variety of means, including using regular software to launch more sophisticated attacks,” ASEC said.
Learn how to stop ransomware with real-time protection
Join our webinar to learn how real-time MFA and service account protection can stop ransomware attacks.
Save my seat!
The use of CHM files as a malware distribution vector is not limited to Chinese actors. A similar attack chain has been employed by the North Korean nation-state group known as ScarCruft to target their southern counterparts against backdoor-targeted hosts.
Actors also known as APT37, Reaper, and Ricochet Chollima have since leveraged LNK files to harvest user credentials and distribute RokRAT malware, which can download additional payloads.









