A significant number of victims in the consumer and corporate sectors in Australia, Japan, the United States and India have been affected by malware known as information-stealing evasive malware. Viper SoftX.
ViperSoftX was first documented in 2020, and in November 2022, cybersecurity firm Avast used malware to distribute a malicious Google Chrome extension that could siphon cryptocurrencies from wallet applications. We have detailed a campaign to
New analysis from Trend Micro reveals that the malware employs “more advanced encryption and basic anti-analysis techniques such as byte remapping and blocking web browser communication.”
ViperSoftX’s arrival vector is typically software cracks or key generators (keygens), but it also uses real non-malicious software as its “carrier”, such as multimedia editors and system cleaner apps.
One of the key steps the malware performs before downloading the first-stage PowerShell loader is a series of anti-virtual machine, anti-monitoring, and anti-malware checks.
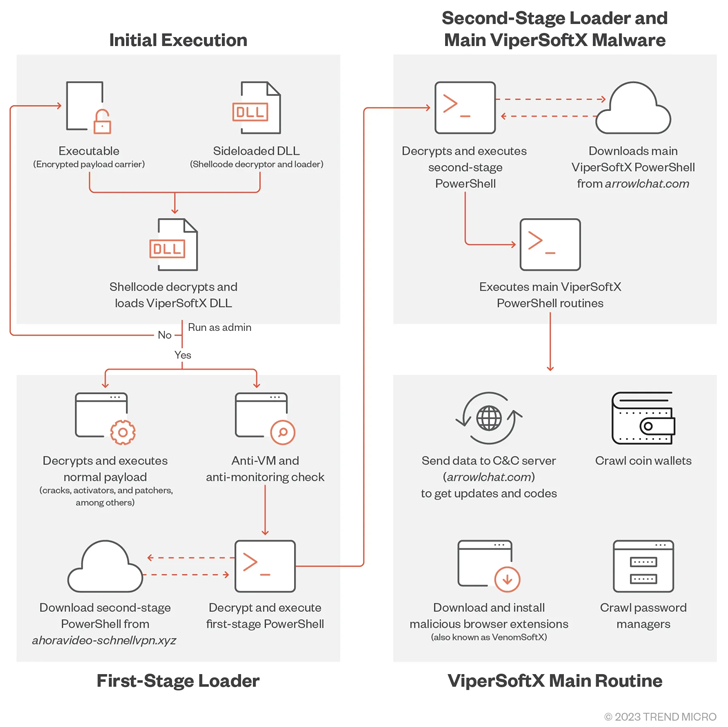
The loader then decrypts and executes the second stage PowerShell script retrieved from the remote server. It then launches its main routine, which installs a malicious browser extension to steal passwords and crypto wallet data.
The primary command and control (C&C) servers used for second-stage downloads have been observed to change on a monthly basis, suggesting the attackers are trying to evade detection.
Learn how to stop ransomware with real-time protection
Join our webinar to learn how real-time MFA and service account protection can stop ransomware attacks.
Save my seat!
“We also use some basic C&C mitigation analysis by forbidding communication using web browsers,” said Trend Micro researcher Don Ovid Ladores, pointing to the existence of KeePass 2 and 1Password password managers. Added an updated version of ViperSoftX Scan to scan.
As a mitigation, users are advised to download software only from official platforms and sources and avoid downloading illegal software.
“By choosing one of the most effective methods of delivering malware to consumers, the cybercriminals behind ViperSoftX ensured a seamless chain of malware execution while remaining under the watchful eye of the authorities. We have enough skills to run,” added Ovid Ladores.









