Ukraine’s Computer Emergency Response Team (CERT-UA) has warned of cyberattacks by Russian nation-state hackers targeting various government agencies in the country.
The phishing campaign was by APT28, also known as Fancy Bear, Forest Blizzard, FROZENLAKE, Iron Twilight, Sednit, and Sofacy.
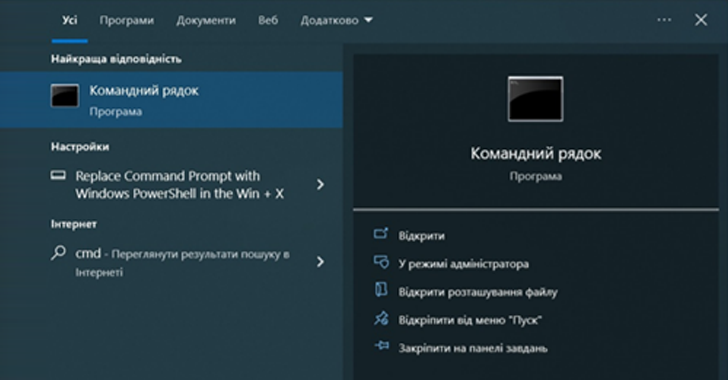
The email message has the subject line “Windows Update” and purportedly contains Ukrainian instructions for running PowerShell commands under the guise of security updates.
Running the script loads and executes the next stage of the PowerShell script. The script is designed to collect basic system information via commands such as tasklist and systeminfo, and extract details via HTTP requests to the Mocky API.

To trick the target into executing commands, the email impersonated a system administrator at the targeted government agency using a fake Microsoft Outlook email account created with the employee’s real name and initials.
CERT-UA recommends that organizations limit the ability of users to run PowerShell scripts and monitor network connections to the Mocky API.
The disclosure comes several weeks after APT28 was linked to attacks that exploited currently patched security flaws in network equipment to conduct reconnaissance and deploy malware against selected targets. rice field.
In an advisory published last month, Google’s Threat Analysis Group (TAG) detailed a credential harvesting operation performed by a threat actor to redirect visitors to a Ukrainian government website to a phishing domain.
A Russian-based hacking crew exploited a critical privilege escalation flaw in Microsoft Outlook (CVE-2023-23397, CVSS score: 9.8) to infiltrate European government, transport, energy, and military sectors. is also involved in
Learn how to stop ransomware with real-time protection
Join our webinar to learn how real-time MFA and service account protection can stop ransomware attacks.
Save my seat!
The development also comes when Fortinet FortiGuard Labs uncovers a multi-stage phishing campaign that utilizes macro-laced Word documents, presumably from Ukraine’s Energoatom, as a lure to deliver the open-source Havoc post-exploitation framework.
“Russian intelligence, military, and law enforcement agencies likely have long-standing tacit understandings with cybercrime threat actors,” cybersecurity firm Recorded Future said in a report earlier this year. I’m here.
“In some cases, these agencies almost certainly maintain established and systematic relationships with cybercrime threat actors through indirect collaboration or recruitment.”











