
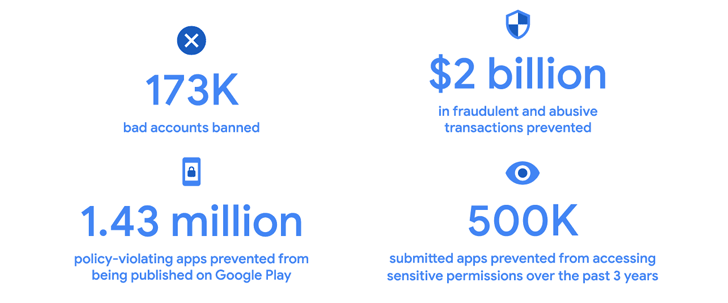
Google has revealed that it has blocked 1.43 million malicious apps from being published on the Play Store in 2022 due to its improved security features and app review process.
Additionally, it says it has banned over 173,000 fraudulent accounts and avoided over $2 billion in fraudulent and abusive transactions through developer features such as the Voided Purchases API, Obfuscated Account ID, and Play Integrity API.
The addition of identity verification methods, such as phone numbers and email addresses, to join Google Play has contributed to a decline in accounts used to publish policies-violating apps, Google noted.
The search giant further states that it has “prevented nearly 500,000 submitted apps from unnecessarily accessing sensitive permissions over the past three years.”
“In 2022, the App Security Improvements program will enable developers to fix 500,000 security exploits affecting 300,000 apps with a combined install base of approximately 250B.” said.
In contrast, Google has blocked 1.2 million policy-violating apps from publishing and banned 190,000 fraudulent accounts in 2021.
The development comes a few weeks after Google enacted a new data deletion policy that requires app developers to give users “quick find options” both inside and outside their apps.
Despite these efforts by Google, cybercriminals continue to find ways to circumvent the security protections of app storefronts and publish malicious and adware apps.
Case in point, McAfee’s mobile research team found 38 games disguised as Minecraft. These games have been installed by his over 35 million users worldwide, mostly located in the United States, Canada, South Korea and Brazil.
While delivering the promised functionality, these gaming apps have been found to embed HiddenAds malware, silently loading ads in the background and generating illicit revenue for their operators.
Some of the most downloaded apps are –
- Blockbox Master Diamond (com.good.robo.game.builder.craft.block)
- Craft Sword Mini Fun (com.craft.world.fun.fun.everyday.block)
- Block Box Skyland Sword (com.skyland.pet.realm.block.rain.craft)
- Craft Monster Crazy Sword (com.skyland.fun.block.game.monster.craft)
- Block Pro Forest Diamond (com.monster.craft.block.fun.robo.fairy)
“One of the most accessible pieces of content for young people using mobile devices is gaming,” McAfee said. “Malware authors are also aware of this and try to hide malicious functionality within their games.”
Complicating matters is the proliferation of Android banking malware that attackers can weaponize to gain access to targeted devices and gather personal information.
Another emerging trend is the use of binding services to trojanize legitimate applications and hide malicious APK payloads. According to Cyble, this technique has been employed by malicious actors to distribute her Android botnet, called DAAM.
Learn how to stop ransomware with real-time protection
Join our webinar to learn how real-time MFA and service account protection can stop ransomware attacks.
Save my seat!
Once installed, the malware functions as ransomware by establishing a connection with a remote server and encrypting files stored on the device using passwords obtained from the server. perform malicious actions.
DAAM also abuses Android’s accessibility services to monitor user activity, record keystrokes, record VoIP calls from instant messaging apps, collect browser history, call logs, photos, screenshots, and SMS messages. Allows harvesting, executing arbitrary code, and opening phishing URLs. .
“Malware authors often use legitimate applications to distribute malicious code to avoid suspicion,” said the cybersecurity firm in an analysis released last month.
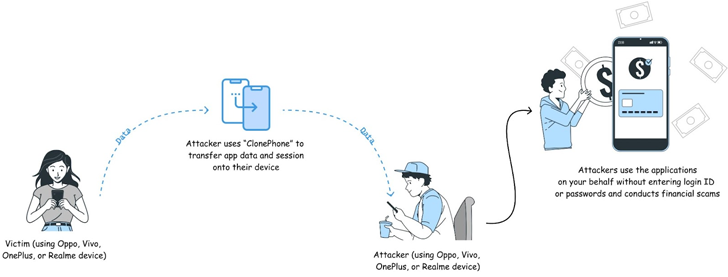
CloudSEK found that several popular Android applications such as Canva, LinkedIn, Strava, Telegram, and WhatsApp do not invalidate or revalidate session cookies after app data is transferred between devices. bottom.
This attack scenario would require the attacker to have physical access to the target phone, but could allow account takeover and unauthorized access to sensitive data.
To mitigate these threats, enable two-factor authentication (2FA) to add an extra layer of account protection, scrutinize app permissions, password protect your device, and never leave it in public places. We recommend that you









