North Korean threat actor known as scar craft As early as July 2022, we began experimenting with using oversized LNK files as a delivery route for the RokRAT malware. This is the same month that Microsoft started blocking macros across Office documents by default.
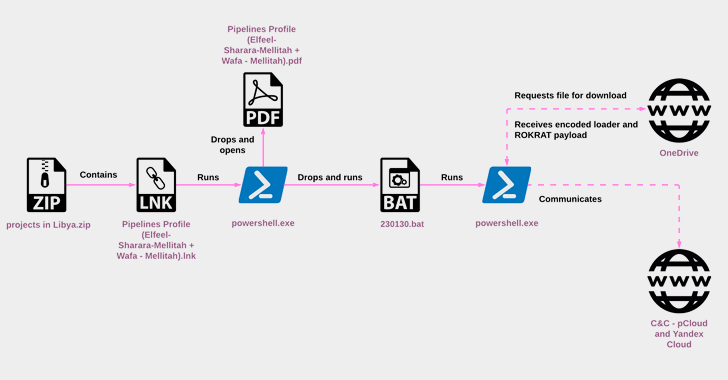
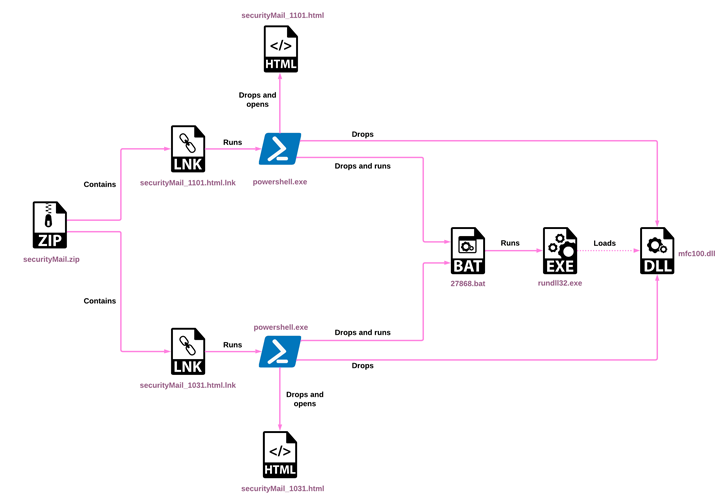
“While RokRAT has remained largely unchanged over the years, its deployment method has evolved and now utilizes archives containing LNK files that initiate a multi-stage infection chain,” said Check Point. says in a new technical report.
“This represents a major trend in the threat landscape where APTs and cybercriminals alike seek to overcome macro blocking from untrusted sources.”
ScarCruft, also known as APT37, InkySquid, Nickel Foxcroft, Reaper, RedEyes, and Ricochet Chollima, has targeted South Korean individuals and entities almost exclusively as part of a spear-phishing campaign designed to deliver an array of custom tools. A threat group that targets .

According to Mandiant, unlike the Lazarus Group and Kimski, the hostile group is overseen by North Korea’s Ministry of State Security (MSS), which is responsible for domestic counter-espionage operations and foreign counterintelligence operations. .
The main malware chosen by this group is RokRAT (aka DOGCALL), which has since been adapted to other platforms such as macOS (CloudMensis) and Android (RambleOn), where the backdoor is actively developed and maintained. indicates that
RokRAT and its variants are capable of performing a variety of activities, including stealing credentials, exfiltrating data, capturing screenshots, gathering system information, executing commands and shellcodes, and managing files and directories. increase.
The collected information, some of which is stored in the form of MP3 files to cover the tracks, is sent back using cloud services such as Dropbox, Microsoft OneDrive, pCloud and Yandex Cloud to disguise command and control. (C2) as legitimate communication.
Other bespoke malware used by this group includes, but is not limited to Chinotto, BLUELIGHT, GOLDBACKDOOR, Dolphin and most recently M2RAT. Commodities such as Amadey, a downloader that can receive commands from attackers to download additional malware, have also been known to use their malware to disrupt attribution.
Last week, the AhnLab Security Emergency Response Center (ASEC) also highlighted the use of LNK files as decoys to activate infection sequences. This file contains PowerShell commands to deploy the RokRAT malware.
While the change in modus operandi shows ScarCruft’s efforts to keep up with the changing threat ecosystem, it still uses malicious macro-based Word documents to drop malware in April 2023. continued, mirroring a similar chain reported by Malwarebytes in January. 2021 years.
Learn how to stop ransomware with real-time protection
Join our webinar to learn how real-time MFA and service account protection can stop ransomware attacks.
Save my seat!
Another attack wave observed in early November 2022 deployed Amadey malware using a ZIP archive containing a LNK file, according to an Israeli cybersecurity firm.
“[The LNK file] This method can trigger an equally effective infection chain with a simple double-click. This chain is more reliable than n-day exploits or Office macros that require an extra click to launch,” said Check Point.
“APT37 continues to pose a sizeable threat, launching multiple campaigns across its platforms and significantly improving its malware delivery methods.”
When Kaspersky revealed a new Go-based malware codenamed SidLevel developed by ScarCruft, the malware was the first to utilize cloud messaging service Aly as a C2 mechanism and used a “widespread network to steal sensitive information from victims. functions.
In its Q1 2023 APT Trends report, the Russian cybersecurity firm said, “The group is targeting individuals associated with North Korea, including novelists, university students, and businessmen who are believed to be transferring funds to North Korea. continue to target.”









