
Cybersecurity researchers have discovered weaknesses in software implementations of the Border Gateway Protocol (BGP) that can be weaponized to achieve a denial of service (DoS) condition on vulnerable BGP peers.
Three vulnerabilities exist in version 8.4 of FRRouting, a popular open source internet routing protocol suite for Linux and Unix platforms. It is currently used by multiple vendors such as NVIDIA Cumulus, DENT and SONiC, creating supply chain risks.
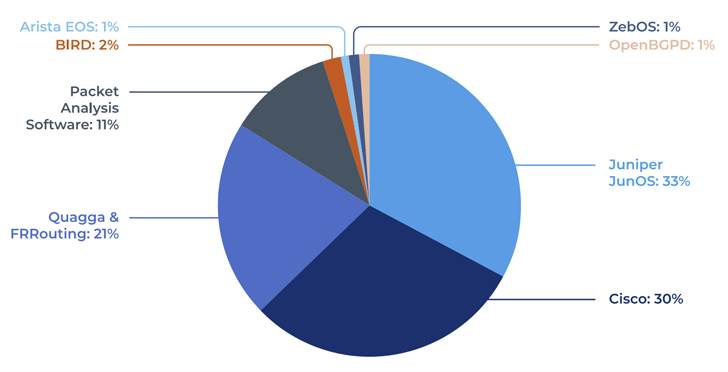
This finding is the result of an analysis of seven different implementations of BGP (FRRouting, BIRD, OpenBGPd, Mikrotik RouterOS, Juniper JunOS, Cisco IOS, and Arista EOS) conducted by Forescout Vedere Labs.
BGP is a gateway protocol designed to exchange routing and reachability information between autonomous systems. It is used to find the most efficient routes for delivering internet traffic.

Here is a list of the three flaws:
- CVE-2022-40302 (CVSS Score: 6.5) – Processing a malformed BGP OPEN message with the Extended Optional Parameters Length option causes an out-of-bounds read.
- CVE-2022-40318 (CVSS Score: 6.5) – Processing a malformed BGP OPEN message with the Extended Optional Parameters Length option causes an out-of-bounds read.
- CVE-2022-43681 (CVSS score: 6.5) – Out-of-bounds read when processing a malformed BGP OPEN message that abruptly ends in an optional length octet.
In a report shared with HackerNews, the company said, “To achieve a DoS condition on a vulnerable BGP peer, attackers have exploited this issue to drop all BGP sessions and routing tables, rendering the peer unresponsive. It’s possible,” he said.
“Repeatedly sending malformed packets can extend a DoS condition indefinitely. The main root cause is that the same vulnerable code pattern causes multiple is copied into the function of
Attackers can spoof valid IP addresses of trusted BGP peers, exploit other flaws or misconfigurations to compromise legitimate peers, or issue specially crafted and unsolicited BGP OPEN messages. There is a possibility.
This is achieved by taking advantage of the fact that FRRouting begins processing the OPEN message (e.g., decapsulating optional parameters) before it has had a chance to check the originating router’s BGP identifier and ASN fields. will be
Learn how to stop ransomware with real-time protection
Join our webinar to learn how real-time MFA and service account protection can stop ransomware attacks.
Save my seat!
Forescout has also made available an open source tool called bgp_boofuzzer. This allows organizations to test the security of their internally used BGP suites and find new flaws in their BGP implementations.
“Modern BGP implementations still have easy outcomes that can be exploited by attackers,” Forescout said. “To reduce the risk of a weak BGP implementation, […] The best recommendation is to patch your network infrastructure devices as often as possible. “
The findings of this study revealed that ESET used routers previously used in business networking environments to hide sensitive data such as corporate credentials, VPN details, encryption keys and other important customer information. It was done a few weeks after discovering that
A Slovak cybersecurity firm said that “data collected from devices, including customer data, router-to-router authentication keys, application lists, etc., when misused, is sufficient to launch a cyberattack.









