Meta has been found to use OpenAI’s ChatGPT as a lure to spread about 10 malware families since March 2023, with more than 1,000 malicious URLs to prevent them from being shared across the service. said to have taken action.
This development comes against the backdrop of the increasing use of fake ChatGPT web browser extensions to steal users’ Facebook account credentials for the purpose of running unauthorized ads from hijacked business accounts. I’m here.
“Threat actors create malicious browser extensions available on official web stores that claim to offer ChatGPT-based tools,” said Meta. “They then promoted these malicious extensions on social media and sponsored search results to trick people into downloading the malware.”

The social media giant said it had blocked repeated multi-pronged malware campaigns called Ducktail for years, adding that it had issued a cease and desist letter to the individuals behind the operation in Vietnam.
At Trend Micro series of tweets Last week, we detailed an information stealer that masqueraded as ChatGPT’s Windows desktop client to extract passwords, session cookies, and history from Chromium-powered browsers. The company says the malware shares similarities with Ducktail.
Besides ChatGPT, attackers have other “hot button issues and popular topics” such as Google Bard, TikTok marketing tools, pirated software and movies, and Windows utilities that trick people into clicking on fake links. has also been observed to migrate to
Guy Rosen, Chief Information Security Officer at Meta, said:
The attack chain is primarily designed to target the personal accounts of users who manage or connect Facebook business pages and advertising accounts.
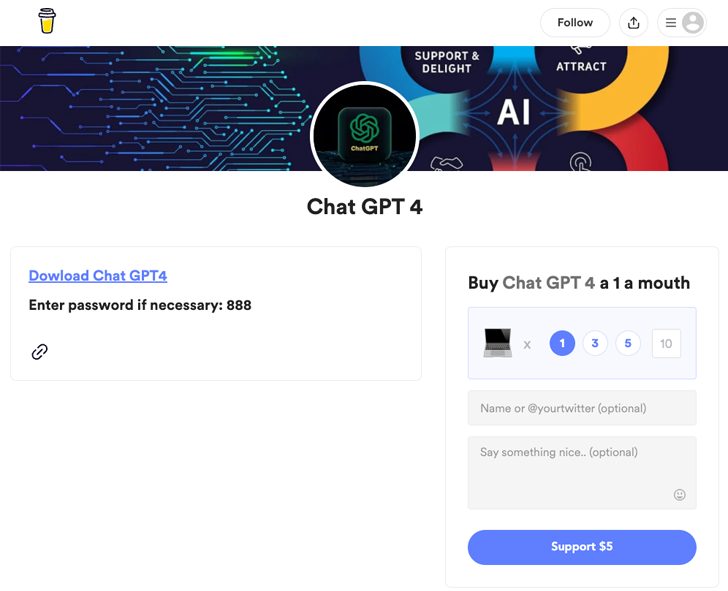
In addition to using social media to spread ChatGPT-themed malicious URLs, the malware can also be used on other platforms such as Buy Me a Coffee, Discord, Dropbox, Google Drive, iCloud, MediaFire, Mega, Microsoft OneDrive, and Trello. Hosted on various legitimate services.
Ducktail wasn’t the only stealer malware detected in the wild. Meta has revealed that it has discovered another new strain called NodeStealer that can loot cookies and passwords from web browsers and eventually compromise Facebook, Gmail, and Outlook accounts.
The malware is believed to have originated in Vietnam, and Meta said within two weeks of its deployment in late January 2023 that it had “sabotaged the malware, allowing potentially targeted people to recover their accounts.” We have taken steps to do so,” he said.
Learn how to stop ransomware with real-time protection
Join our webinar to learn how real-time MFA and service account protection can stop ransomware attacks.
Save my seat!
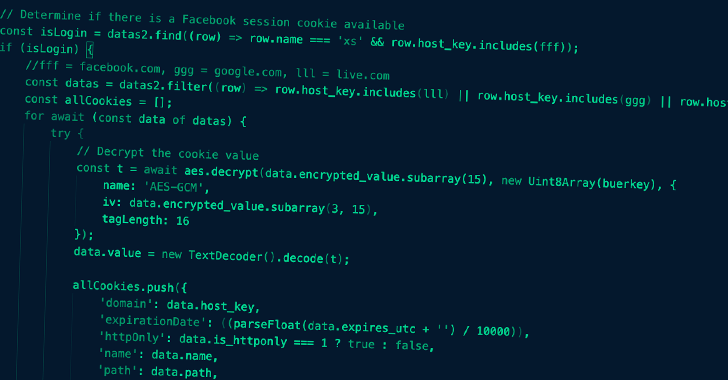
According to samples analyzed by the company, NodeStealer binaries are distributed via Windows executables masquerading as PDF and XLSX files with filenames related to marketing or monthly budgets. Upon opening the file, it delivers JavaScript code designed to exfiltrate sensitive data from Chromium-based browsers.
NodeStealer gets its name from the fact that it uses the Node.js cross-platform JavaScript runtime environment bundled with the main payload to set persistence and run the malware. As of February 27, 2023, no new artifacts have been observed.
“After obtaining Facebook credentials from the target’s browser data, the malware uses it to make multiple illegitimate requests to Facebook URLs to enumerate account information related to ads.” Meta said. “Stolen information allows attackers to assess a user’s ad account and use it to run fraudulent ads.”
In an attempt to stay under the radar of the company’s anti-abuse system, the targeted user’s device makes illegitimate requests to the Facebook API to masquerade as legitimate activity.
To combat such threats, Meta allows users to identify and remove malware, allows businesses to see connected Business Manager accounts, access credit lines and change business administrators. He said he’s launching a new support tool that will guide you when to request additional authentication.











