New Android subscription malware named Fleckpe was discovered on the Google Play Store, and the cumulative number of downloads since 2022 has exceeded 620,000.
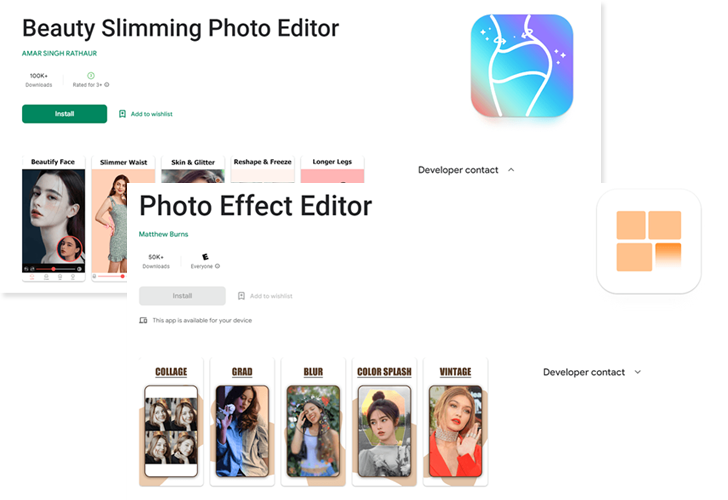
According to Kaspersky, which identified 11 apps on its official app storefront, the malware disguised itself as a legitimate photo-editing app, camera, and smartphone wallpaper pack. The app has since been removed.
While the operation primarily targeted users in Thailand, telemetry data collected by a Russian cybersecurity firm revealed victims in Poland, Malaysia, Indonesia, and Singapore.

These apps deliver promised functionality to avoid red flags, but hide their true purpose under the hood. Here is the list of problematic apps –
- Beauty Camera Plus (com.beauty.camera.plus.photoeditor)
- Beauty Photo Camera (com.apps.camera.photos)
- Beauty Slimming Photo Editor (com.beauty.slimming.pro)
- Fingertip Graffiti (com.draw.graffiti)
- GIF Camera Editor (com.gif.camera.editor)
- HD 4K Wallpapers (com.hd.h4ks.wallpaper)
- Impressionist Pro Camera (com.impressionism.prozs.app)
- Microclip Video Editor (com.microclip.vodeoeditor)
- Night Mode Camera Pro (com.urox.opixe.nightcamreapro)
- Photo Camera Editor (com.toolbox.photoeditor)
- Photo Effects Editor (com.picture.pictureframe)
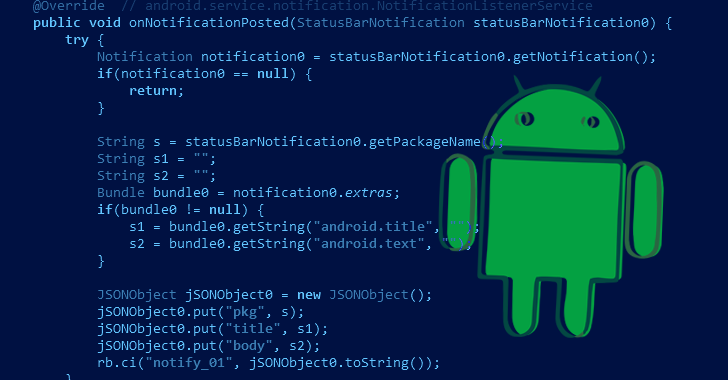
“When the app launches, it loads a highly obfuscated native library containing a malicious dropper that decrypts and executes the payload from the app’s assets,” said Kaspersky researcher Dmitry Kalinin.
The payload is designed to connect to a remote server and send information about the compromised device, such as mobile country code and mobile network code. The server then responds with a paid subscription page.
The malware then attempts to subscribe on the user’s behalf by opening a page in an invisible web browser window and abusing the permissions to access the notification and obtain the verification code required to complete the procedure. will do.
In a sign of Fleckpe’s active development, recent versions of the malware have moved most of their malicious functionality into native libraries to avoid detection by security tools.
Learn how to stop ransomware with real-time protection
Join our webinar to learn how real-time MFA and service account protection can stop ransomware attacks.
Save my seat!
“The payload currently just intercepts the notification and displays a web page, acting as a bridge between the native code and the Android component required to purchase the subscription,” said Kalinin.
“Unlike native libraries, the payload has few evasive capabilities, but malicious actors have added code obfuscation to the latest versions.”
This isn’t the first time subscription malware has been spotted on the Google Play store. Fleckpe joins other fleeceware families such as Joker (aka Bread or Jocker) and Harly to subscribe infected devices to unwanted premium services and perform fraudulent billing.
While such apps are not as dangerous as spyware or financial Trojans, they can generate fraudulent charges, gather various sensitive information from their operators, and serve as entry points for more malicious malware. may be diverted to
If anything, the findings indicate that attackers continue to find new ways to sneak apps into official app marketplaces to expand their campaigns, allowing users to download and access apps. Care must be taken when granting permissions.
“Trojans are becoming more sophisticated, successfully bypassing many anti-malware checks implemented by the market and remaining undetected for long periods of time,” said Kalinin.











