
Product security plays a central role in the fast-paced cybersecurity environment. DevSecOps swoops in, seamlessly integrating security practices into his DevOps and empowering teams to tackle challenges. Dive into DevSecOps and explore how collaboration can give your team an edge to fight cybercriminals.
Application Security and Product Security
Unfortunately, application security teams often step in late in the development process. Maintain security levels in published software and ensure the integrity and confidentiality of data consumed or produced. It focuses on protecting data flow, isolating environments with firewalls, and implementing strong user authentication and access controls.
The product security team aims to ensure the inherent trustworthiness of applications. Recommend tools and resources and make them available to developers and operators. In the DevSecOps approach, each team is responsible for the security of the applications they create. These teams apply secure coding techniques, perform static and dynamic tests to ensure your applications are not abused, keep your sensitive data safe, and ensure your applications can handle load and attacks.
Enhanced product security
SecOps guilds intervening in product teams typically play a cross-functional role, ensuring consistency across projects for technical and financial reasons. They encourage DevOps teams to use security tools of choice and ensure proper implementation. This step streamlines security resources and further collaboration allows each DevOps team to benefit from the work and experience of the other team.
We can think of an easy way to use collaboration tools to make your product more secure.
1 — Plan Mitigation
In the event of a security incident or vulnerability, knowing that potential damage is identified and controlled is imperative for SecOps. This is why providing profiling information and how users can sandbox their software ranks among the best things users can do. You can start by using containers with limited rights, but you can go a step further by designing a security profile. Providing an AppArmor profile or his Seccomp filter leaves both the potential attacker and the attack surface highly limited and known even if the app is compromised. Our incident response and forensics teams appreciate this.
2 — Identify anomalous behavior
Developers can identify error signals during application development, usually in the form of error messages in logs. By categorizing error messages and correlating them with anomalous behavior in shared artifact repositories on Github or other collaborative platforms, DevOps teams can determine whether a particular error occurrence signifies anomalous or aggressive behavior. can. Subsequent analysis is much easier with structured logs.
3 — Compare, Count, Correlate
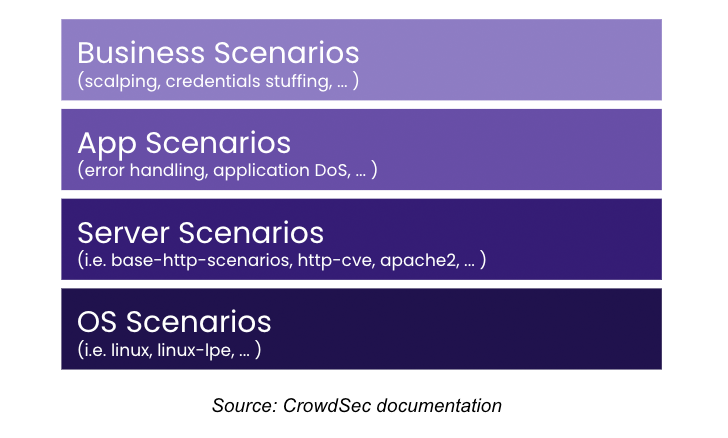
These indicators should be compared, counted and correlated. Multiple failed authentication attempts, or attempts to send malformed data or document formats are reliable markers of unexpected behavior. Relying on a centralized tool like a SIEM for this task can go against some DevOps principles. Instead, application decisions should be made quickly and locally, as needed and at the pace of the application. There are a number of description languages that can generate behavioral scenarios directly from developer-provided data with minimal integration into your CI/CD process.
4 — Take action
Once deviant behavior is identified, steps should be taken to protect the application. Actions may include slowing flows, revoking an attacker’s access, or banning IPs that can harm application processing power. While those using SOAR can use SOAR to respond quickly to security events, others may prefer decentralized decision-making using tools such as: Crowdsec Interface with web front ends, authentication servers, or firewalls.
5 — Share security signals
SecOps often works with multiple DevOps teams, so tools that recognize anomalous behavior and provide a step-by-step response are helpful. By sharing security signals, each DevOps team can benefit from other teams’ experiences. By associating a scenario with each code library to characterize anomalous behavior, you save time each time another team uses that library. Scenarios stored in local repositories are accessible to all users, allowing you to create a security framework for each application that integrates scenarios. Ultimately, securing applications relies heavily on the experience previously gained by all her DevSecOps teams.
6 — Share more
Collaborative tools enable sharing of attack signals, for example using frameworks such as MITER ATT&CK. An offensive source banned for offensive behavior in one application can be banned in all company applications.For example, each CrowdSec security engine Signals can be shared on a local or global scale so attacker IPs are recognized and blocked instantly, protecting applications and data and reducing the burden on security infrastructure.
grow stronger together
DevSecOps teams work together to protect applications and foster collaboration for the highest reliability and data security. Employing tools that leverage collective experience provides better protection against the growing horde of cybercriminals. By sharing attack signals and leveraging crowdsourced information, organizations can work together to become stronger and face cyberthreats. Ultimately, teamwork is everything, proving that we are an unstoppable force against cyberattacks.
To see a demo of the collaboration tools mentioned in the article, please visit: https://booking.crowdsec.net/book-a-demo
Note: This article was written by Jerome Clauzade of CrowdSec.









