Government agencies in Central Asia have been targeted by sophisticated espionage campaigns using a previously undocumented variant called malware. down x.
In a report shared with The Hacker News, Bitdefender says activity remains high and there is evidence of the involvement of a Russian-based threat actor.
A Romanian cybersecurity firm said it first detected malware in a highly targeted attack aimed at a foreign government agency in Kazakhstan in late 2022. Another attack was then observed in Afghanistan.
The use of diplomat-themed decoy documents and the focus of the campaign on data theft suggest the involvement of state-sponsored groups, although the exact identities of the hacking group remain unknown at this stage. .

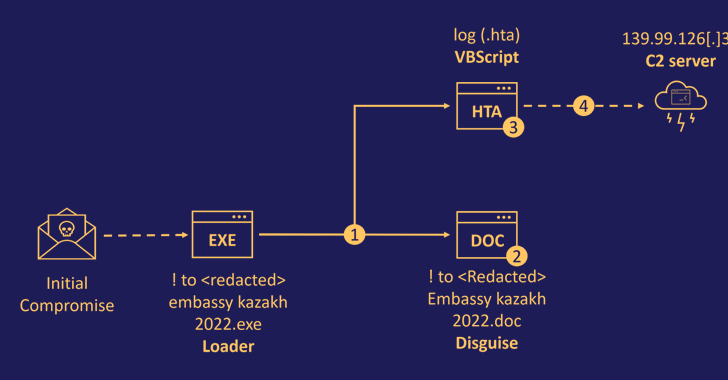
The initial vector of entry for the campaign is suspected to be a spear-phishing email containing a booby-trap payload, a loader executable masquerading as a Microsoft Word file.
Upon opening the attachment, it extracts two files containing a decoy document that is presented to the victim while a malicious HTML application (.HTA) with embedded VBScript code runs in the background.
The HTA file is designed to establish a connection with a remote command and control (C2) server to retrieve the payload for the next stage. The exact nature of the malware is unknown, but it is said to be a backdoor to establish persistence.
This attack is also notable for its use of various custom tools to perform post-exploitation activities. This is also –
- Two C/C++ based binaries (wnet.exe and utility.exe) for enumerating all resources on the network.
- A Python script (help.py) that receives instructions to establish an infinite communication loop with a C2 server and steal files with specific extensions, delete files created by other malware, capture screenshots, and
- C++ based malware (diagsvc.exe aka DownEx) designed primarily to steal files to C2 servers
Learn how to stop ransomware with real-time protection
Join our webinar to learn how real-time MFA and service account protection can stop ransomware attacks.
Save my seat!
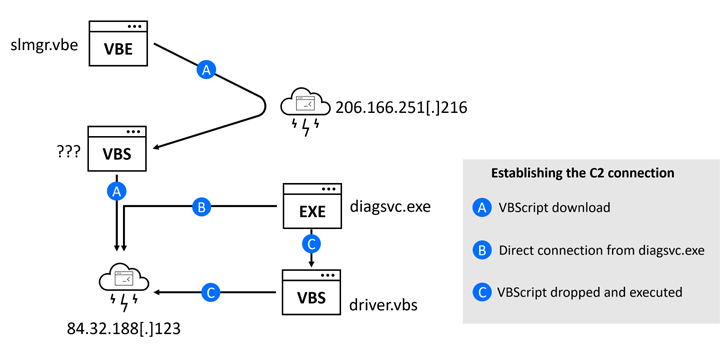
Two other variants of DownEx were also discovered. The first variant runs an intermediate VBScript to collect files and send them in the form of a ZIP archive.
Another version downloaded via a VBE script (slmgr.vbe) from a remote server avoids C++ for VBScript but retains the same functionality as the former.
“This is a fileless attack. The DownEx script runs in memory and never hits the disk,” said Bitdefender. “This attack highlights the sophistication of modern cyberattacks. Cybercriminals are finding new ways to increase the credibility of their attacks.”











