
On Tuesday, the US government announced a court-approved suspension of its global network. snake Used by the Russian Federal Security Service (FSB).
Dubbed “the most sophisticated cyber espionage tool,” Snake is the handiwork of a Russian state-owned group called Turla (aka Iron Hunter, Secret Blizzard, SUMMIT, Uroburos, Venomous Bear, Waterbug) and the U.S. government A unit within center 16 of the FSB.
This threat actor has a track record of focusing on entities in Europe, the Commonwealth of Independent States (CIS), and NATO member states, with recent activity including Middle Eastern countries seen as a threat to Russia-backed nations. to expand its footprint. region.
“For nearly 20 years, this unit has […] used a version of the Snake malware to extract classified documents from hundreds of computer systems in at least 50 countries belonging to governments of North Atlantic Treaty Organization (NATO) countries, journalists, and other targets of interest to the Russian Federation. stole the ‘ said the Justice Department.
“After stealing these documents, Turla stole them through an unwitting covert network of Snake-infected computers in the United States and around the world.”

This neutralization was orchestrated using a tool codenamed PERSEUS created by the United States Federal Bureau of Investigation (FBI) as part of an effort called Operation MEDUSA. With this tool, authorities issued commands to the malware to “overwrite its own critical components.” “On an infected machine.
By means of self-destruct instructions designed after decrypting and decoding the malware’s network communications, “the Snake implant disabled itself without affecting the host computer or legitimate applications on the computer,” the agency said. says.
According to an advisory released by the U.S. Cybersecurity and Infrastructure Security Agency (CISA), Snake was designed as a covert tool for long-term intelligence gathering on high-priority targets, allowing adversaries to peer-to-peer Allows you to create a (P2P) network. ) network of compromised systems around the world.
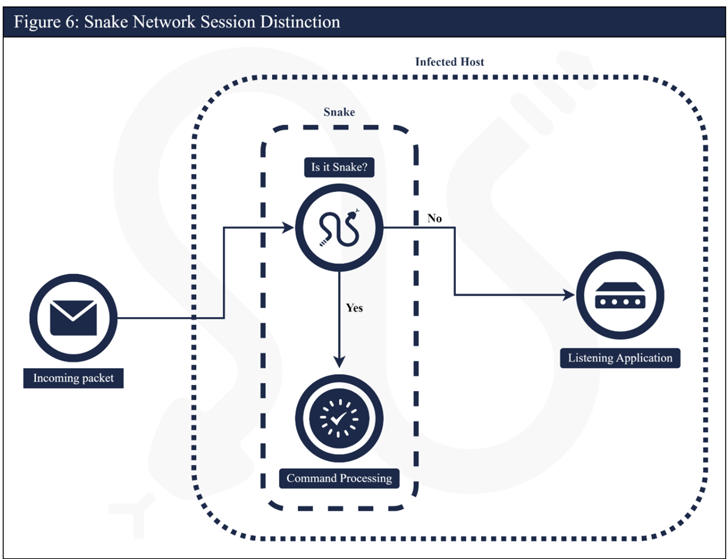
Additionally, multiple systems within the P2P network acted as intermediary nodes, routing disguised operational traffic to and from the Snake malware embedded in the FSB’s ultimate target, making the activity difficult to detect. rice field.
C-based cross-platform malware further employs custom communication methods to add new layers of stealth, efficiently inject or modify components to enhance functionality, and maintain persistent access to valuable information It features a modular architecture that allows
“Snake demonstrates careful software engineering design and implementation, and given its complexity, the implant contains surprisingly few bugs,” CISA said, adding that the implant’s first He added that the version was developed around early 2004.
“The name Urobros is apt because the FSB cycled it through almost constant stages of upgrades and redevelopments.”
Learn how to stop ransomware with real-time protection
Join our webinar to learn how real-time MFA and service account protection can stop ransomware attacks.
Save my seat!
Infrastructure associated with the Kremlin-backed group has been identified in more than 50 countries in North America, South America, Europe, Africa, Asia, and Australia, but its targets have been assessed as more tactical. , government networks, research facilities and journalists. .
Sectors victimized within the United States include education, small businesses, media organizations, and critical infrastructure sectors such as government facilities, financial services, critical manufacturing, and telecommunications.
Despite these setbacks, Turla remains an aggressive and formidable adversary, unleashing a variety of tactics and tools to breach targets on Windows, macOS, Linux, and Android.
The development comes just over a year after US law enforcement and intelligence agencies disarmed a modular botnet known as Cyclops Blink controlled by another Russian state actor called Sandworm. .









