
A security vulnerability has been revealed in the popular WordPress plugin Essential Addons for Elementor, which can be exploited to elevate privileges on affected sites.
This issue was tracked as CVE-2023-32243 and was resolved by the plugin maintainers in version 5.7.2, which shipped on May 11, 2023. Elementor’s Essential Addons have over 1 million active installs.
“This plugin contains an unauthenticated privilege escalation vulnerability that allows an unauthenticated user to elevate privileges to the privileges of any user on a WordPress site,” Patchstack researcher Rafie Muhammad said. said.
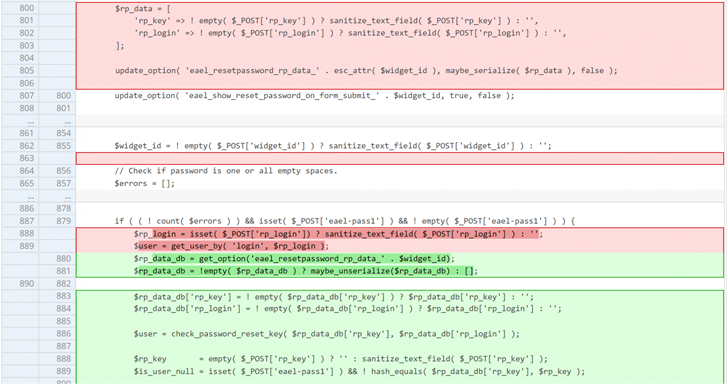
Successful exploitation of this flaw could allow an attacker to reset the password of any user, as long as the malicious party knows the username. This shortcoming is believed to exist since version 5.4.0.
This can have serious repercussions as this flaw can be weaponized to reset the password associated with the administrator account and take full control of the website.
“This vulnerability occurs because the password reset functionality does not validate the password reset key and directly changes the password for the specified user,” Muhammad noted.

This disclosure comes more than a year after Patchstack revealed another critical flaw in the same plugin, which could have been exploited to execute arbitrary code on compromised websites. .
The findings also follow the discovery of a new wave of attacks targeting WordPress sites since late March 2023, aimed at injecting the notorious SocGholish (aka FakeUpdates) malware.
SocGholish is a persistent JavaScript malware framework that acts as an initial access provider to facilitate the delivery of additional malware to infected hosts. The malware was distributed via a drive-by download masquerading as a web browser update.
The latest campaign detected by Sucuri was found to leverage compression techniques using a software library called zlib to hide the malware, reduce its footprint, and evade detection.
“Adversaries are continually evolving their tactics, techniques and procedures to evade detection and extend the lifespan of their malware campaigns,” said Sucuri researcher Denis Sinegubko.
“The SocGholish malware is a prime example, where attackers have changed their approach in the past to inject malicious scripts into compromised WordPress websites.”
Learn how to stop ransomware with real-time protection
Join our webinar to learn how to stop ransomware attacks using real-time MFA and service account protection.
Reserve your seat!
Not just Sock Golish. In this week’s tech report, Malwarebytes details a malvertising campaign that serves adult website visitors with pop-under ads that simulate fake Windows updates that drop an “in2al5d p3in4er” (a.k.a. disabled printer) loader. bottom.
Jerome Segura, director of threat intelligence at Malwarebytes, said, “The scheme is very well designed as it relies on the web browser to display a full-screen animation very similar to what you’d expect from Microsoft. ‘ said.
The loader, documented last month by Morphisec, checks the system’s graphics card to determine if it’s running in a virtual machine or in a sandbox environment, ultimately ending up in the information-stealing malware Aurora. designed to launch
According to Malwarebytes, the campaign has resulted in 585 victims over the past two months, and the actor has also been implicated in other tech support scams and Amadey bot command and control panels.









