Several security vulnerabilities have been identified in the cloud management platforms associated with three industrial cellular router vendors that may expose operational technology (OT) networks to external attacks.
The findings were announced by Israeli industrial cybersecurity company OTORIO at the Black Hat Asia 2023 conference last week.
11 vulnerabilities “allow remote code execution and complete control over hundreds of thousands of devices and OT networks, in some cases not actively configured to use the cloud” “There is a possibility.
Specifically, cloud-based management solutions offered by Sierra Wireless, Teltonika Networks, and InHand Networks for remotely managing and operating devices have shortcomings.

Successful exploitation of this vulnerability could pose significant risks to industrial environments, allowing attackers to bypass security layers, steal sensitive information, or remotely execute code on internal networks. It becomes possible to
Worse, this issue can be weaponized to gain unauthorized access to devices in the network and perform malicious operations such as shutdown with elevated permissions.
This is made possible by three different attack vectors that can be exploited to compromise and hijack cloud-managed IIoT devices through cloud-based management platforms.
- Weak asset registration mechanism (Sierra Wireless): An attacker could scan unregistered cloud-connected devices, leverage the AirVantage online warranty checker tool to obtain serial numbers, register them to managed accounts, and execute arbitrary commands. there is.
- Security configuration flaw (InHand network): An unprivileged user could leverage the command injection flaws CVE-2023-22601, CVE-2023-22600, and CVE-2023-22598 to execute remote code with root privileges and issue a reboot command. , may push a firmware update.
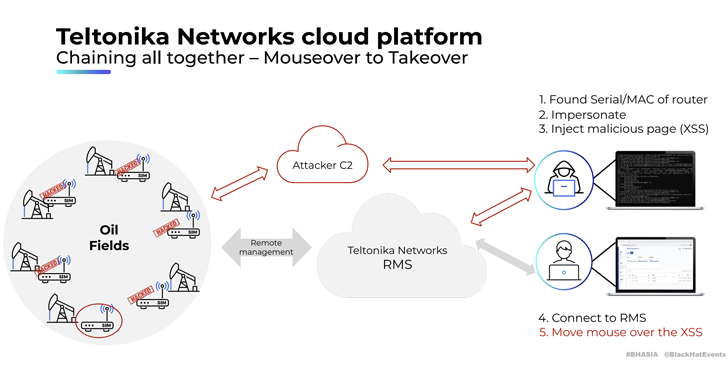
- External APIs and Interfaces (Teltonika Networks): Threat actors have exploited multiple issues identified in the Remote Management System (RMS) to “expose sensitive device information and device credentials, allow remote code execution, and allow uncontrolled access on the network. exposed connected devices that are known to be malicious and allow spoofing of legitimate devices.
The six flaws (CVE-2023-32346, CVE-2023-32347, CVE-2023-32348, CVE-2023-2586, CVE-2023-2587, and CVE-2023-2588) affecting Teltonika Networks are It was discovered after a “comprehensive investigation”. The study was carried out in collaboration with Claroti.
Learn how to stop ransomware with real-time protection
Join our webinar to learn how to stop ransomware attacks using real-time MFA and service account protection.
Reserve your seat!
“When attackers successfully exploit these industrial routers and IoT devices, they can do a variety of things to the compromised device or network, such as monitoring network traffic, stealing sensitive data, hijacking internet connections and accessing internal services. It could have an impact,” they said.
OTORIO said cloud-managed devices pose a “huge” risk to the supply chain, with a single vendor’s breach potentially acting as a backdoor to access multiple OT networks at once.
This development allows cybersecurity firms to provide attackers with a direct path to internal OT networks, potentially compromising critical infrastructure with 38 security threats to wireless Industrial Internet of Things (IIoT) devices. A little over 3 months after revealing the above flaws.
“As the deployment of IIoT devices becomes more prevalent, it’s important to recognize that their cloud management platforms may become targets for threat actors,” said security researcher Roni Gavrilov. “A single he IIoT vendor platform, when exploited, could act as a ‘pivot point’ for attackers, gaining access to thousands of environments at once.”











