Government agencies, military organizations, and civilian users in Ukraine and Poland have been targeted as part of a series of campaigns aimed at stealing sensitive data and gaining persistent remote access to infected systems.
This intrusion set lasted from April 2022 to July 2023, leveraging phishing lures and decoy documents to deploy a downloader malware called PicassoLoader that acts as a conduit to launch the Cobalt Strike Beacon and njRAT.
“The attack used a multi-stage infection chain that started with a malicious Microsoft Office document, most commonly Microsoft Excel and PowerPoint files,” Cisco Talos researcher Vanja Svajcer said in a new report. format was used.” “Following this, the executable downloader and payload may be hidden in an image file, making detection more difficult.”
Some of the activity is believed to be attributed to an actor called GhostWriter (aka UAC-0057 or UNC1151), whose priorities are said to align with the Belarusian government.
It is worth noting that some of these attacks have already been documented over the past year by the Ukraine Computer Emergency Response Team (CERT-UA) and Fortinet FortiGuard Labs, one of which involves macros. A PowerPoint document was used to deliver the Agent Tesla malware in July 2022. .
The infection chain aims to lure the victim into enabling macros. The VBA macro is designed to drop a DLL downloader known as PicassoLoader, which then visits an attacker-controlled site to load the next stage, which is a legitimate image file with the final file embedded. Get the payload. Malware.
The disclosure comes as CERT-UA details a number of phishing campaigns distributing the SmokeLoader malware and smishing attacks aimed at gaining unauthorized control of targeted Telegram accounts.
Last month, CERT-UA uncovered a cyber espionage campaign targeting Ukrainian state institutions and journalists. The campaign utilizes email and instant messengers to distribute files, and once initiated a PowerShell script called LONEPAGE is run to retrieve the following information: -stage browser stealer (THUMBCHOP) and keylogger (CLOGFLAG) payloads.
Shielding Against Insider Threats: Mastering SaaS Security Posture Management
Worried about insider threats? We’ve got you covered! Join us for this webinar to explore practical strategies and proactive security secrets using SaaS Security Posture Management.
join today
GhostWriter is one of many threat actors targeting Ukraine. This includes the Russian nation-state group APT28. APT28 has been observed using her HTML attachments in phishing emails urging recipients to change her UKR.NET and Yahoo! Suspicious activity has been detected in your account, so it changes your password, redirects you to a fake landing page, and finally steals your credentials.
The development has also been described by hackers affiliated with the Russian Military Intelligence Service (GRU) as a “standard five-step strategy” as “a deliberate effort to increase the speed, scale and intensity of attacks” in a destructive operation against Ukraine. ” was also adopted. .
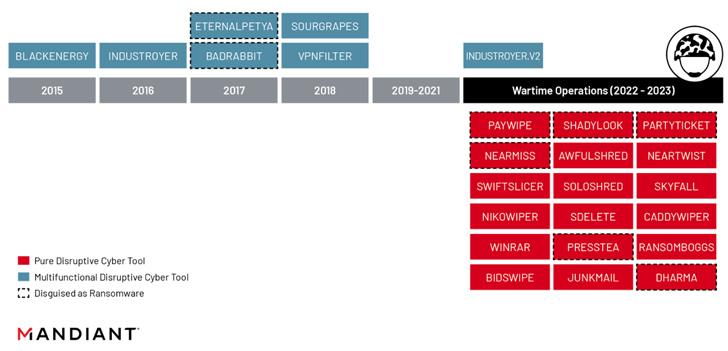
This includes leveraging on-edge infrastructure to gain initial access, land-based reconnaissance, lateral movement, and information theft to limit the malware footprint and avoid detection. It involves creating permanent privileged access using techniques away from Via a Group Policy Object (GPO), deploy the wiper and telegram its actions via the hacktivist persona on Telegram.
“The advantages offered by this strategy are particularly well-suited to a fast-paced, highly contested operating environment, where Russia’s wartime objectives may have guided the GRU’s chosen tactical course of action,” said Mandiant, who owns Google. It shows that there is a lot of potential,” he said.