Arrest, seizure, exposure and detention. These are just a few of the ways police and prosecutors around the world have cracked down on the biggest cybercriminal activity of the year. Even if that means resorting to novel and unconventional methods. From billions of bitcoins hidden under floors to teenage hackers gatecrashing a Fortune 500 network, this year saw some of the most shocking breaches and some of the most high-profile concerns. did.
As we wrap up 2022, we look back at the cybercriminals we lost this year.
Sanctions and Seizures Hit the Crypto Scene
US authorities scored some big wins against cryptolaundering in 2022. Earlier this year, the Justice Department announced that it had seized more than $3.6 billion in bitcoin from him and arrested him in a 2016 hack of cryptocurrency exchange Bitfinex. Married couple suspected of money laundering.
A married couple — Ilya Lichtenstein, 34, and Heather Morgan, 31 — could face up to 25 years if convicted of conspiring to launder money and defraud the U.S. government. face imprisonment.
Later that year, the Office of Foreign Assets Control (OFAC), which is responsible for cracking down on sanctions violations within the U.S. Treasury Department, announced the launch of a decentralized cryptocurrency mixing service responsible for enabling billions of dollars worth of cryptocurrencies. announced that it has authorized Tornado Cash. Laundry through its platform.
Tornado Cash, along with other mixers such as AlphaBay, allows customers to hide the origin of their cryptocurrencies as they participate in transactions in exchange for commissions. Mixing potentially identifiable or tainted cryptocurrency funds with others to obfuscate the origin and destination of the cryptocurrency. Experts estimate that over $1.5 billion in criminal proceeds, including ransomware and fraud, have been laundered through Tornado Cash so far.
US dox claims to be member of Conti ransomware
In August, the US government shared suspected images of the Conti ransomware operator known as “Target.” The program also used his four other purported members of Conti, known as “Trump”, “Dandis”, “Professor” and “Leshaev”, for information leading to the identification and location of the target. provided up to $10 million.
The State Department said Conti has carried out more than 1,000 ransomware attacks targeting US and international critical infrastructure. Most recently, the gang broke into her 27 government offices in Costa Rica and demanded a $20 million ransom.
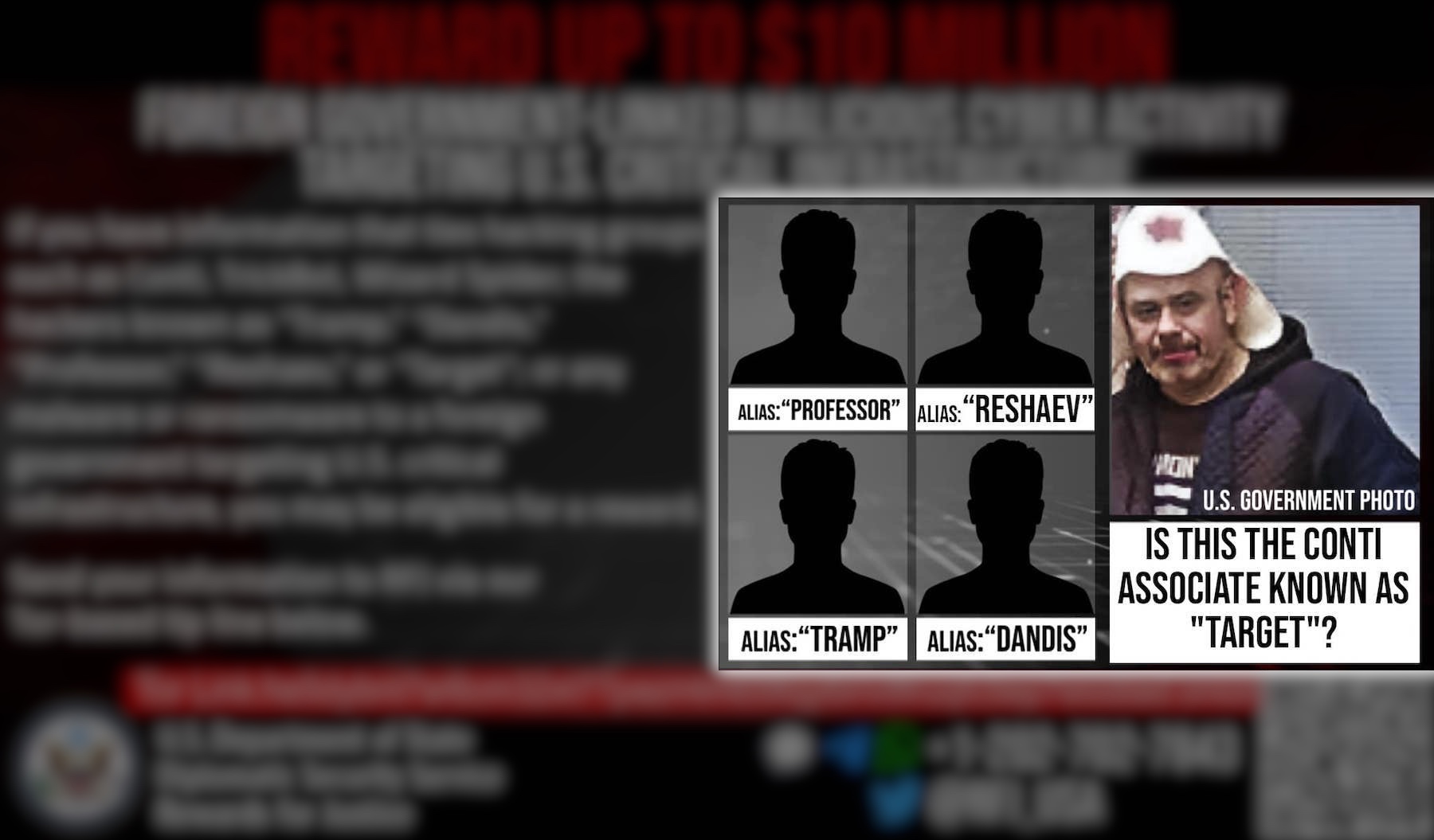
Image credit: Department of State (handout)
Another gang to be devastated in 2022 was the ransomware gang Netwalker. This includes attacks on the University of California, San Francisco, which paid a ransom demand of more than $1 million, and cyber threat startup Cygilant. Ransomware attacks involving NetWalker paid out $46 million between August 2019 and January 2021, according to cryptocurrency analysis firm Chainalysis.
In October, Sebastien Vachon-Desjardins, 34, from Quebec, was convicted in a Florida court in October after pleading guilty to charges related to his involvement with NetWalker. His Vachon-Desjardins, who worked as an IT consultant for Canadian Public Works and Government Services, was arrested by Canadian police in January 2021 and sentenced to seven years in prison. During a raid on his home, law enforcement officers found and seized his 719 Bitcoins and $790,000 of his Canadian currency.
James Zong, the hacker who stole billions of dollars of Bitcoin from the Silk Road
In a surprising yet unexpected conclusion to one of the government’s longest-running cyber scandals, the mystery of the missing billions of dollars in notorious dark web drug marketplace Silk Road has been solved. . In November, the U.S. Federal Bureau of Investigation discovered $3.36 billion worth of bitcoin hidden in popcorn cans under the floorboards of a bathroom closet in a hacker’s home nearly a decade ago. Prosecutors have indicted a hacker named Georgia resident James His Zong. A plea bargain with the federal government confiscated vast amounts of cash in cryptocurrency, along with $600,000 in cash and other precious metals.
Somewhat confusingly, Zhong is the second hacker to finally hand over the stolen billions of dollars of Silk Road, albeit at a lower exchange rate than today. In 2020, a hacker who went by the alias Individual X confiscated another large cache of Silk Road bitcoins that he had stolen years earlier in the 2012-2013 hacking spree. Even though long after Silk Road founder Ross Ulbricht was in jail, how the federal government stole the money and how they found the hackers remained a secret.

The partial contents of popcorn cans contain memory cards containing billions of cryptocurrencies and other precious metals. Image credit: Department of Justice (handout)
Raccoon Stealer operator charged with stealing tons of passwords
In October, U.S. authorities indicted a Ukrainian national for involvement in the Raccoon Infostealer malware-as-a-service operation that infected millions of computers worldwide. Online Mark with his handle name ‘Raccoon Thief’ His Sokolovski is the primary administrator of the malware he used to steal over 50 million unique credentials and identification documents from victims worldwide. accused of playing a major role. From February 2019.
Sokolowski has been charged with computer fraud, wire fraud, money laundering and identity theft, and faces up to 20 years in prison if convicted. Sokolovski is in Amsterdam awaiting extradition to the United States.
Sokolovsky’s arrest has led to a rise in new Mars stealer campaigns, including mass targeting of Ukraine in the weeks following the Russian invasion, and massive efforts to infect victims through malicious advertising. But in November, the security research and hacking startup told TechCrunch that there was a coding flaw that allowed the operators of the Mars Stealer malware to lock themselves out of their servers, freeing their victims. Discovered.
WhatsApp hacking tech seller pleads guilty
Signal jammers, Wi-Fi interception tools, WhatsApp hacking tools. These are some of the federal court admissions that a Mexican businessman sold for commercial and personal reasons. The Justice Department has accused Carlos Guerrero of arranging for the sale of hacking tools to Mexican politicians and using other equipment he sold to intercept calls from US rivals. It shows that states and governments aren’t the only ones with espionage technology at their disposal.
Lapsus$ rounds up once, twice
The Lapsus$ gang made notoriety in 2022. A data extortion group that first emerged a year ago, he soon had many high-profile victims, including Okta, Microsoft, Nvidia, and Samsung.
The gang once seemed invincible, but many of its members were arrested in March of this year. In a statement to TechCrunch at the time, City of London Police confirmed seven of his arrests, ranging from the age of 16 to the age of 21, have been made in connection with Lapsus$.
News of the arrest comes hours after Bloomberg reports revealed that the Oxfordshire, England-based teenager was a suspected ringleader of the Lapsus$ group. A 16-year-old boy who uses his moniker “White” or “Bleach Bass” online believes he is a key figure in Lapsus$, researchers investigating the gang’s recent hacks said. Bloomberg was able to track down the suspected hacker after his personal attack. The information was published online by rival hackers. A few weeks later, British police announced they had charged two of his teenagers with multiple cyberattacks.
No more SSNDOB, the marketplace for stolen social security numbers
In June, US authorities announced the shutdown of SSNDOB, a notorious marketplace used to trade the personal information of millions of Americans, including Social Security Numbers (SSNs).
This landmark operation was carried out by the FBI, IRS and DOJ with the assistance of the Cyprus police, in which the authorities seized four domains hosting the SSNDOB marketplace.
According to prosecutors, SSNDOB has generated more than $19 million in revenue by listing the personal information of approximately 24 million people in the United States, including names, dates of birth, SSNs and credit card numbers. Chainalysis separately reported that the market had received about $22 million worth of bitcoin in over 100,000 transactions since April 2015, but believed the market had been active for several years before the eventual seizure. It is
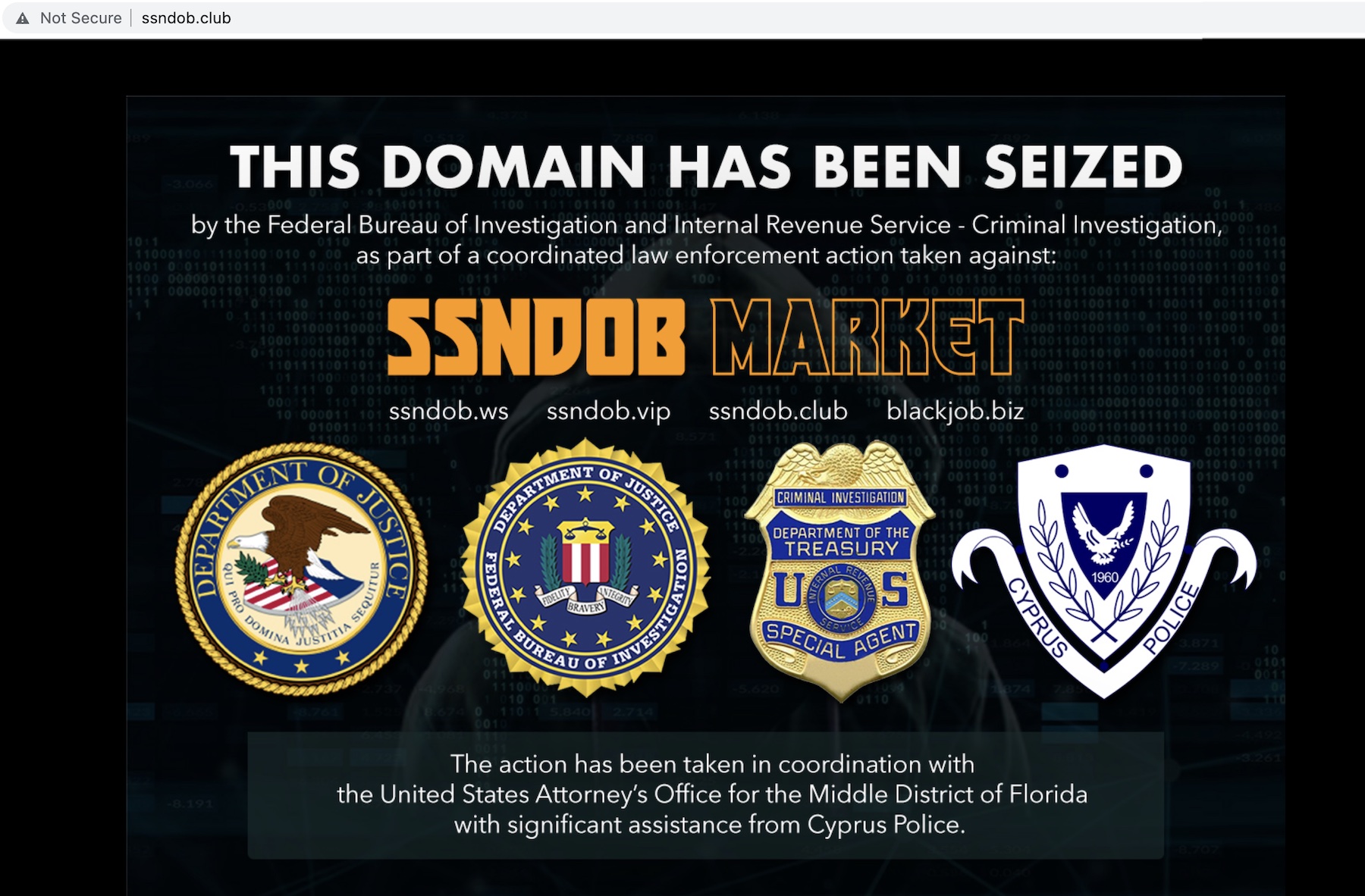
FBI seizure notice for SSNDOB shortly after the site was shut down by federal authorities. Image credit: TechCrunch (screenshot)
Former Amazon Engineer Convicted in Capital One Data Heist
Also in June, Paige Thompson, a former engineer in Amazon’s cloud division, was found guilty of breaching the personal and financial information of CapitalOne’s 100 million customers in 2019. It affected credit scores, limits, stolen balances, and even one million Canadians. It has been accused of compromising cloud storage and of several other companies, including Vodafone, Ford, and an Ohio car agency. Prosecutors said the former Amazon engineer “didn’t take her a day to share the data she stole.” As such, Thompson was sentenced to serve time and was able to avoid prison.
REvil’s main operator handed over to US
After a brazen ransomware attack against Kaseya spread to hundreds of downstream customers, with a $10 million bounty on the horizon, it was only a matter of time before the REvil ransomware group’s luck ran out. Vasinskyi was arrested in Poland in October, then arraigned and extradited to Dallas, Texas, where he was charged with computer hacking and fraud for alleged involvement in REvil. He is one of two other alleged members of REvil who have been indicted by U.S. prosecutors. It was only after the FBI recovered the decryption key that the victim regained access to the encrypted files.
UK arrests teenager involved in Uber and GTA hacks
In September, police in London said a 17-year-old teenager suspected of being involved in high-profile violations at ride-hailing giants Uber and Rockstar Games was charged with computer misuse and breach of bail. confirmed.
These hacks are two of the hottest in 2022. Uber believed a hacker affiliated with Lapsus$ was responsible for the attack, but was forced to take several internal tools offline while banning the hacker from its network. Shortly before Uber’s Slack system went offline, an Uber employee received a message saying, “I am a hacker and Uber has had a data breach.” The hackers also reportedly said Uber drivers should receive higher wages.
In the case of Rockstar Games, the attackers (aka “TeaPots”) gained access to internal Rockstar Games messages on Slack and early code for an unannounced Grand Theft Auto sequel, as well as access to employee logins. claimed to have been obtained by acquiring credentials.